- Escape discovers shadow APIs through agentless OSINT and AI fingerprinting; StackHawk discovers APIs from source code repositories and OpenAPI specs.
- StackHawk offers transparent pricing from $42/contributor/month with a free tier; Escape uses custom enterprise pricing with no self-service option.
- Escape runs 100+ dedicated GraphQL security tests (introspection abuse, batching attacks, authorization flaws); StackHawk supports GraphQL but with less specialized depth.
- StackHawk integrates with GitHub Actions, GitLab CI, Jenkins, CircleCI, and Azure DevOps for per-build scanning; Escape focuses on periodic external scans.
- Escape tests business logic vulnerabilities (BOLA, BFLA, IDOR) that StackHawk’s CI-embedded model may miss; StackHawk covers REST, GraphQL, SOAP, and gRPC protocols.
Which Is Better: Escape or StackHawk?#
Escape is an agentless API security platform that discovers shadow APIs and tests for business logic flaws. StackHawk is a developer-first DAST tool that embeds API security testing directly into CI/CD pipelines. Both sit at the intersection of the DAST tools landscape and the API security tools landscape .
Escape and StackHawk both target API security, but they approach the problem from different angles. Escape is an agentless platform that excels at external API discovery and business logic testing.
It uses AI-powered fingerprinting and OSINT techniques to find APIs you may not even know are exposed, then tests them for OWASP Top 10 risks , broken object-level authorization (BOLA) , and other advanced flaws.
StackHawk is a developer-first DAST tool built to run inside CI/CD pipelines, catching vulnerabilities on every build before code reaches production.
The choice comes down to your primary concern. If your biggest worry is shadow APIs and complex authorization flaws across a sprawling API surface, Escape gives you visibility that pipeline-only tools cannot.
If your goal is to give every developer fast security feedback on every pull request with predictable per-seat pricing, StackHawk delivers that workflow with minimal friction.
Both tools represent the next generation of API security testing and are far more effective for modern API architectures than legacy DAST scanners that were designed for server-rendered web applications.
What Are the Key Differences?#
| Feature | Escape | StackHawk |
|---|---|---|
| License | Commercial | Commercial (Freemium) |
| Pricing | Custom (enterprise-quoted) | From $42/contributor/month |
| API Discovery | Agentless external discovery (OSINT, AI fingerprinting) | Repository-based discovery via SCM integration |
| REST API Testing | Yes | Yes |
| GraphQL Testing | Yes (100+ dedicated tests) | Yes |
| SOAP Testing | No | Yes |
| gRPC Testing | No | Yes |
| Business Logic Testing | Yes (BOLA, BFLA, IDOR) | Limited |
| OWASP Top 10 Coverage | Yes | Yes |
| CI/CD Integration | GitHub Actions, GitLab CI | GitHub Actions, GitLab CI, Jenkins, CircleCI, Azure DevOps |
| Authentication Support | Automated (token-based, OAuth) | YAML-based auth config (OAuth, API keys, multi-step) |
| Deployment Model | Agentless SaaS | Agent in CI/CD pipeline |
| SARIF Output | Yes | Yes |
| API Spec Import | OpenAPI, GraphQL schemas | OpenAPI, GraphQL schemas, HAR files |
| Remediation Guidance | AI-assisted fix suggestions | AI-generated developer guidance |
| Scan Speed | Minutes (external scan) | Runs per build (pipeline speed) |
| Shadow API Detection | Yes (core feature) | Limited (SCM-based mapping) |
| Compliance Reporting | Yes (SOC 2, PCI DSS) | Yes (compliance dashboards) |
| Free Tier | No | Free plan available |
| Maintained By | Escape (Paris, France) | StackHawk (Denver, USA) |
Neither Escape nor StackHawk offers API runtime protection. Both are scanning and testing tools that find issues before deployment, not inline platforms that block live attacks.
Buyers needing runtime detection of OWASP API Top 10 attacks (BOLA, BFLA, injection) on production traffic should evaluate Salt Security , Akamai API Security , or Wallarm separately — they cover the runtime layer that comes after the testing layer Escape and StackHawk operate on.
Escape vs StackHawk: How Do They Compare?#
API Discovery#
This is where Escape differentiates itself most clearly. Escape scans externally using subdomain enumeration, AI-powered fingerprinting, and open-source intelligence to build an inventory of every API exposed across your infrastructure.
This catches shadow APIs, forgotten endpoints , and services that were never documented — the kind of targets that attackers find first.
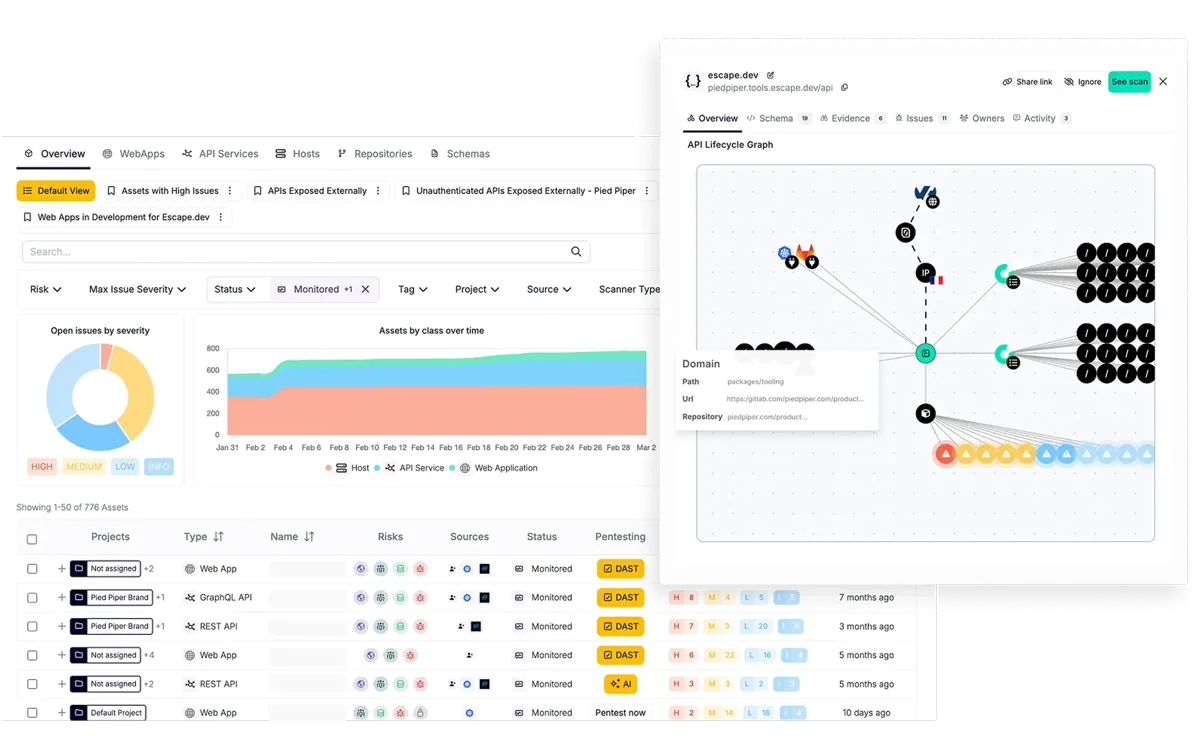
StackHawk takes a code-repository approach instead. It integrates with your source control to map your application landscape, identifying APIs from your codebase and OpenAPI specifications.
This works well for known, actively developed services but will not catch APIs that exist outside your main repositories or were deployed by other teams without documentation.
For organizations that already have tight control over their API inventory, StackHawk’s approach is sufficient. For those with sprawling microservice architectures, acquisitions, or legacy services, Escape’s external discovery fills a gap that internal-only tools leave open.
Testing Depth and Vulnerability Coverage#
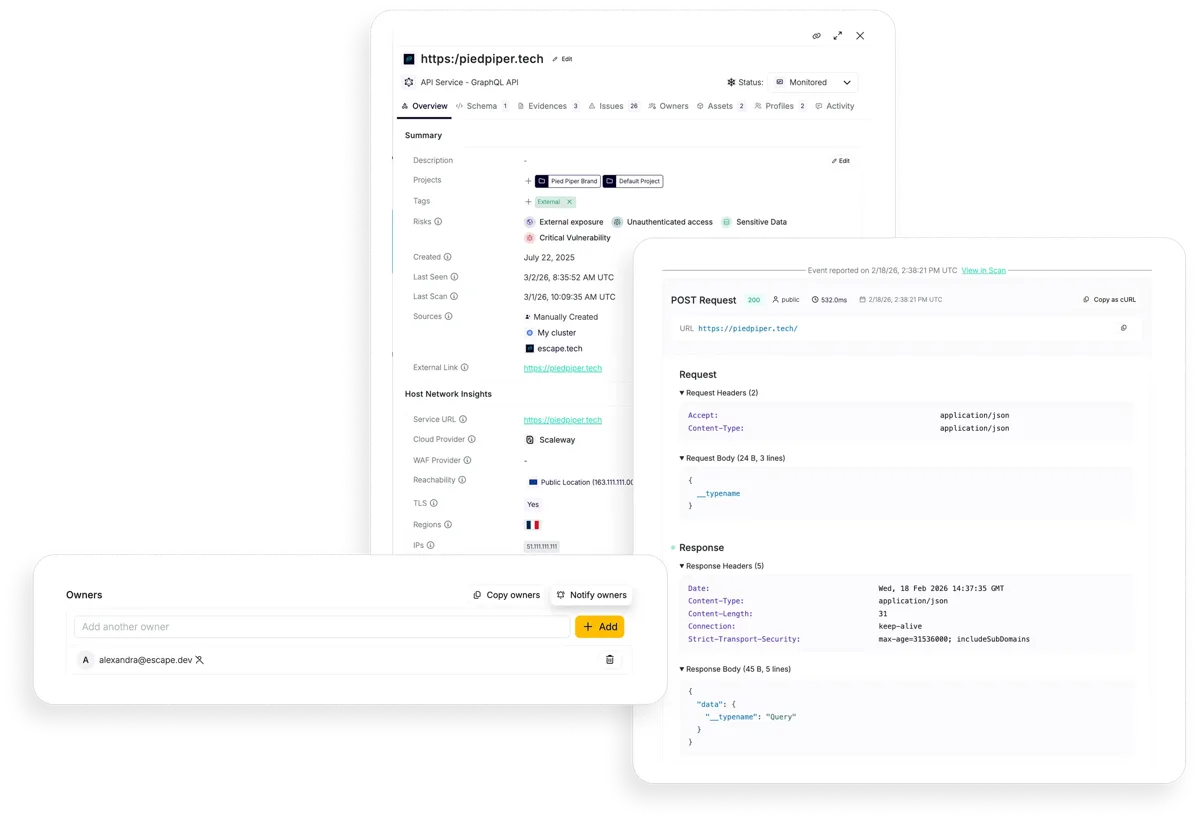
Escape’s scanner was built specifically for API security and goes beyond standard OWASP checks.
It tests for broken object-level authorization (BOLA), broken function-level authorization (BFLA) , insecure direct object references (IDOR), and other business logic flaws that require understanding how API endpoints relate to each other.
The GraphQL engine runs over 100 security tests covering introspection abuse, query batching attacks, depth limiting, and field-level authorization.
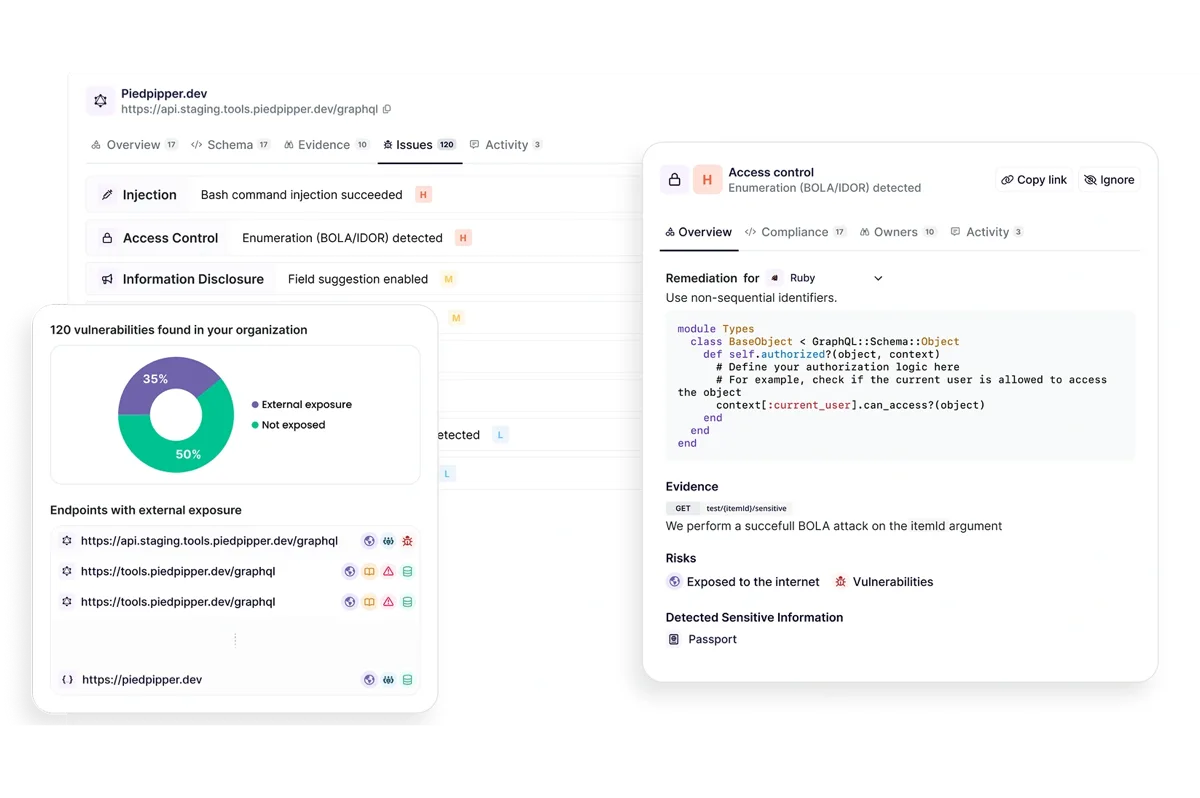
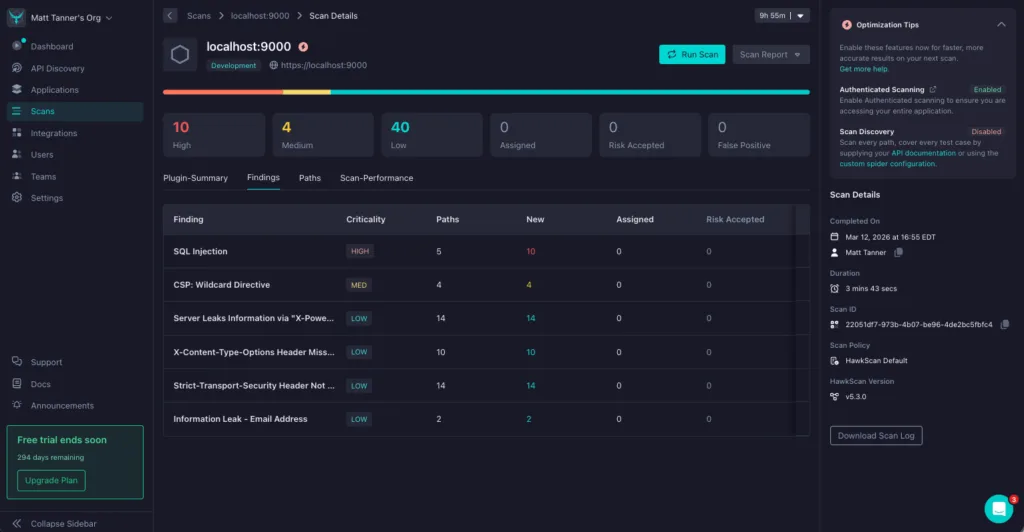
StackHawk covers the OWASP Top 10 for APIs and performs solid dynamic testing against REST, GraphQL, SOAP, and gRPC endpoints.
Its breadth of protocol support is wider than Escape’s, and it handles authenticated scanning well through YAML-configured auth flows.
Where it is less deep is in the business logic layer — StackHawk is effective at finding injection flaws, misconfigurations, and known vulnerability patterns, but it does not probe authorization boundaries as aggressively as Escape.
CI/CD Integration and Developer Workflow#
StackHawk was designed from the ground up to live inside the development pipeline. It runs as part of every CI/CD build, giving developers immediate feedback when they introduce a security issue.
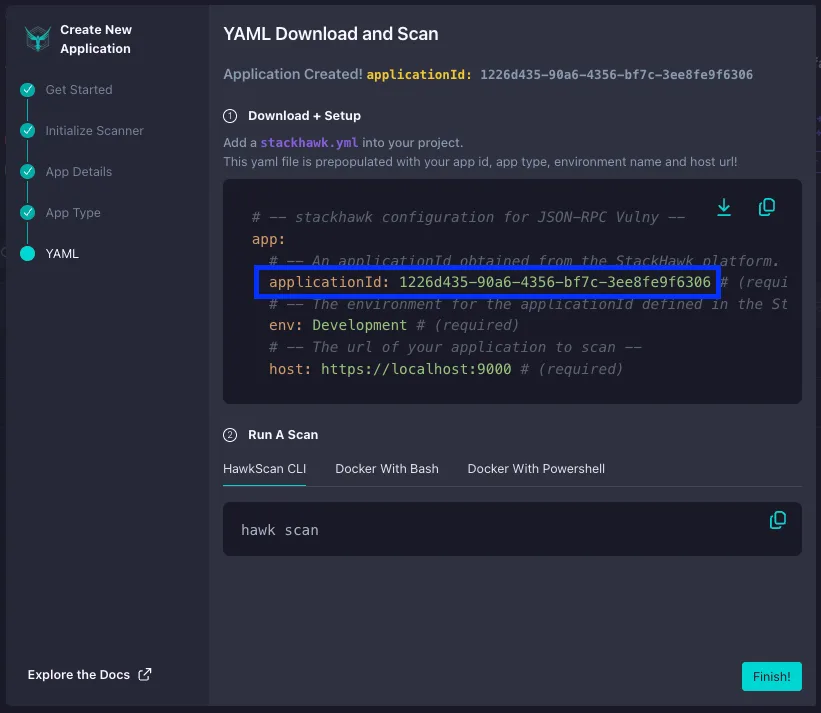
Integration is available for GitHub Actions , GitLab CI/CD, Jenkins, CircleCI, Azure DevOps, and AWS pipelines. Authentication is configured as code in YAML, which means scan configurations live in version control alongside the application.
Escape integrates with GitHub Actions and GitLab CI but its primary model is periodic or on-demand scanning rather than per-build execution. The agentless architecture means there is no agent to install or maintain, which simplifies deployment for security teams but provides less tight coupling with individual developer workflows.
StackHawk gives developers a faster feedback loop. Escape gives security teams broader visibility.
The right choice depends on whether you prioritize developer experience or broad coverage.
Pricing and Accessibility#
StackHawk publishes transparent pricing: $42/month per code contributor on the Pro plan, $59/month on Enterprise, with custom pricing for teams over 50 developers. Unlimited scans, unlimited applications, no concurrency restrictions.
A 14-day free trial of the enterprise plan is available for evaluation.
Escape uses custom enterprise pricing. There is no free tier or self-service plan.
This positions Escape as a mid-market to enterprise purchase that typically requires a sales conversation.
For startups and small teams, StackHawk is the more accessible option. For larger organizations with budget for specialized API security tooling, Escape’s pricing reflects the depth of its discovery and testing capabilities.
Reporting and Compliance#
Both tools produce scan results in standard formats including SARIF for integration with GitHub and GitLab code scanning.
Escape provides compliance-oriented reporting aligned with SOC 2, PCI DSS, and other frameworks, which appeals to organizations with audit requirements.
StackHawk offers compliance dashboards and integrates findings into developer workflows through Jira, Slack, and other collaboration tools.

Escape’s reporting leans toward security team consumption — risk dashboards, API inventory views, and executive summaries. StackHawk’s reporting is more developer-facing, with remediation guidance written in the developer’s language and easy re-scan workflows to validate fixes.
When Should You Choose Escape vs StackHawk?#
Choose Escape if:
- You need to discover shadow APIs and undocumented endpoints across your infrastructure
- Business logic vulnerabilities (BOLA, BFLA, IDOR) are a primary concern
- Your organization has a large GraphQL API surface requiring deep testing
- You want agentless deployment with no agents to install or maintain
- Your security team needs compliance-ready reporting for audits
- You have enterprise budget and prefer deep API security coverage
Choose StackHawk if:
- You want DAST running on every CI/CD build with fast developer feedback
- Transparent per-contributor pricing fits your budget model
- You need to test across REST, GraphQL, SOAP, and gRPC protocols
- Developer experience and self-service remediation are top priorities
- You want authentication-as-code in YAML stored alongside your application
- Your team is smaller and needs a free tier to get started
- Integration with Jenkins, CircleCI, or Azure DevOps is required
For more AppSec Santa comparisons, see the API security tools and DAST tools categories. Buyers who want methodology context before settling on a tool should read my API security testing guide , and the broader DAST-for-APIs context is covered in DAST tools for APIs .
Escape vs StackHawk pricing#
StackHawk publishes a public pricing structure on stackhawk.com with a free tier and paid tiers starting at roughly $42 per contributor per month, scaling on a per-contributor basis with annual commitments and enterprise volume discounts available through sales.
The free plan is intended for solo developers and small teams scoping the platform; the paid tiers add concurrent scans, advanced authentication patterns, and team management. Pricing details are subject to change on the vendor site, so confirm current numbers on stackhawk.com before purchase.
Escape uses a contact-sales model. The escape.tech pricing page does not publish per-environment or per-API rates, and quotes are issued based on the size of the API estate, the depth of business-logic testing required, and whether external attack surface management is included alongside the core scanner.
Free trials are available through the vendor’s sales team rather than as a self-serve signup.
The pricing models reflect the buyer profile each vendor targets. StackHawk’s per-contributor model fits engineering teams paying out of an R&D budget; Escape’s enterprise quote model fits security teams paying out of a centralized AppSec budget.
Procurement cycles for Escape typically run 30–60 days for new buyers, while StackHawk’s self-serve tier means small teams can be running scans on the same day they sign up.
Escape vs StackHawk FAQ#
**Is Escape or StackHawk better for GraphQL? ** Escape has dedicated GraphQL discovery, introspection-based testing, and a GraphQL-specific business-logic check set, which makes it the stronger pick for teams running large GraphQL surfaces.
StackHawk added GraphQL coverage through its HawkAI feature set, with introspection support and query depth controls; it covers the basics but Escape’s depth on GraphQL is the differentiator most buyers cite.
**Do either tool offer runtime protection? ** No. Both Escape and StackHawk are DAST and API testing platforms that operate before deployment or in CI.
For inline runtime detection of OWASP API Top 10 attacks on production traffic, evaluate Salt Security , Akamai API Security , or Wallarm — they cover the runtime layer that sits after the testing stage.
**Can I run both in CI/CD? ** Yes. Both ship native plugins for Jenkins, GitHub Actions, GitLab CI, CircleCI, and Azure DevOps, with pull-request integrations that fail builds on findings above a configured severity.
Some teams run StackHawk on every build for fast developer feedback and Escape on a scheduled cadence (nightly or weekly) for the deeper business-logic and shadow-API coverage; the two are complementary more often than directly competitive.
**Which is better for OpenAPI / REST APIs?
** StackHawk’s heritage is built on the OWASP ZAP engine, which makes it strong on REST API testing driven by OpenAPI specs uploaded into the platform . Escape parses OpenAPI specs as one input among several
It also derives endpoints from external discovery and traffic so the answer depends on whether the team has clean specs (StackHawk fits the developer flow) or a sprawling estate where the spec is incomplete (Escape fills the gap).
**Which works better with non-web APIs? ** Both support gRPC and SOAP alongside REST and GraphQL. StackHawk’s per-protocol testing is configured through HawkScan’s authentication-as-code YAML; Escape covers the same protocols through the platform’s discovery and contract-aware scanning.
For non-HTTP transports outside this set (binary protocols, async messaging), neither vendor is the right tool — runtime API security platforms with traffic-mirror deployments cover that surface better.
Frequently Asked Questions
Is Escape better than StackHawk?
How much does Escape cost compared to StackHawk?
Can I use both Escape and StackHawk?
Which tool is better for GraphQL API security?
Which tool supports more API protocols?

Written & maintained by
Suphi CankurtEight years on the vendor side of application-security sales — thousands of evaluations and demos. I started AppSec Santa in 2022 to put that insider view to work for buyers. Independent of any vendor, paid by none, and honest about what fits whom.