APIs are the primary attack surface for most modern applications — and the OWASP API Top 10 catalogues the most exploited API vulnerabilities from broken object level authorization to server-side request forgery.
Open-source tools now cover API security across the entire development lifecycle: static analysis of the OpenAPI specification, source code scanning, and dynamic testing against running endpoints. This guide covers the seven most effective open-source and free-tier API security tools and explains where each fits in your security workflow.
Why specialized API security tooling?
Open-source API security tools are software that test REST and GraphQL APIs for vulnerabilities such as broken authentication, injection, and authorization flaws — without requiring commercial licenses.
They differ from general-purpose DAST scanners because APIs use JSON instead of HTML, enforce authentication via JWT or OAuth rather than cookies, and define their attack surface through endpoint schemas rather than crawlable links.
This structural difference means general DAST tools miss API-specific vulnerabilities.
Broken Object Level Authorization (BOLA)
, the top item on the OWASP API Top 10, requires understanding that /api/users/123/orders and /api/users/456/orders are the same endpoint pattern — and testing whether user 123 can access user 456’s orders. Traditional DAST crawlers do not understand that relationship.
The tools below are built with API-specific attack patterns in mind: they import OpenAPI/Swagger specifications, understand REST and GraphQL structure, and test for the vulnerabilities that break APIs specifically.
Top 7 open-source API security tools
1. OWASP ZAP
ZAP (Zed Attack Proxy) is the most widely used open-source DAST tool and the strongest free option for API security testing.
It supports REST API testing via OpenAPI, Swagger 2.0, and SOAP WSDL import. The ZAP API Scan profile actively tests imported endpoints for authentication issues, injection vulnerabilities, security header gaps, and common API misconfigurations.
What ZAP does well: OpenAPI import automatically creates a sitemap of all documented endpoints, removing the need to crawl APIs manually. The Automation Framework lets you configure ZAP as a YAML pipeline step without custom scripting.
Its active scan covers OWASP API Top 10 checks, and the Docker image (ghcr.io/zaproxy/zaproxy:stable) enables headless execution in GitHub Actions and GitLab CI.
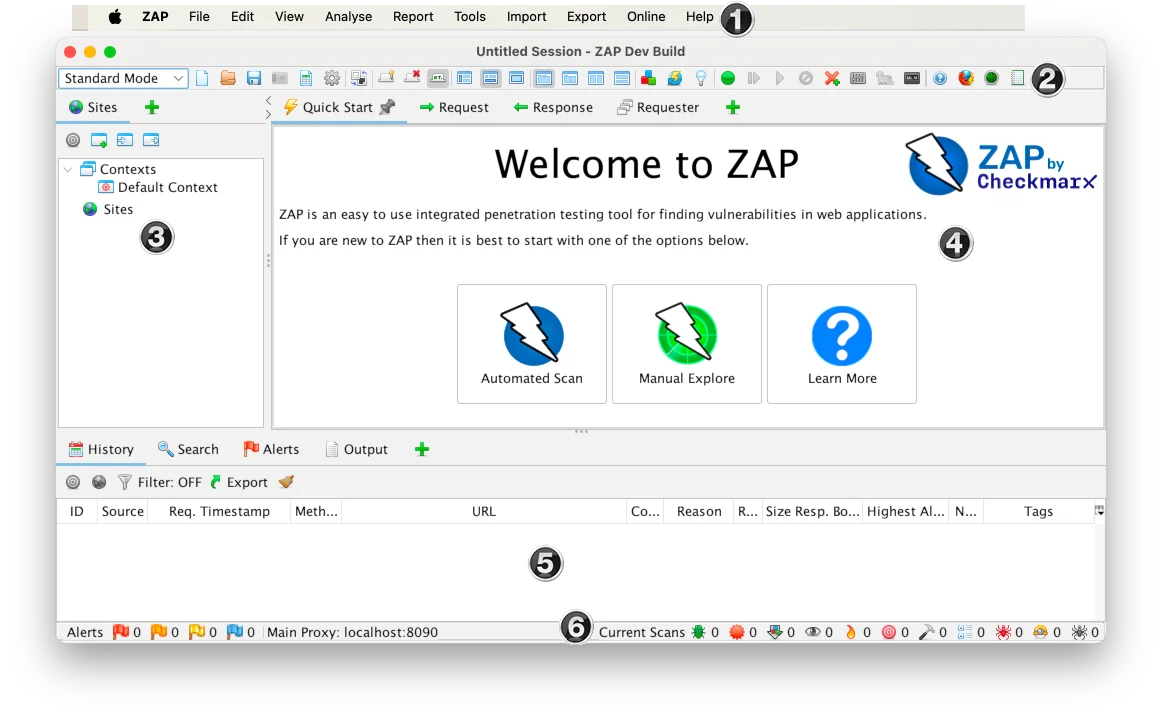
Where ZAP falls short: ZAP was designed as a web application proxy first — the API-specific experience requires configuration. GraphQL support is partial compared to REST. Scan results require expertise to triage; alert volume can be high on first runs.
Best fit: Any team that needs DAST coverage of REST APIs in CI/CD without a commercial license. ZAP is the open-source DAST standard. See the API security testing guide for ZAP pipeline configuration patterns.
2. Nuclei
Nuclei is an open-source template-based scanner from ProjectDiscovery that has become essential for API security testing. With over 26,000 GitHub stars and 12,000+ community templates, it covers API vulnerabilities including JWT algorithm confusion, BOLA/IDOR patterns, GraphQL introspection exposure, SSRF sinks, and API key exposure.
What Nuclei does well: Template granularity — you run exactly the checks relevant to your API stack, not a broad scan. The template ecosystem grows daily with community contributions. GraphQL-specific templates cover introspection, query depth attacks, and batch query abuse. Nuclei runs fast against many endpoints in parallel and integrates into CI/CD as a single binary command.
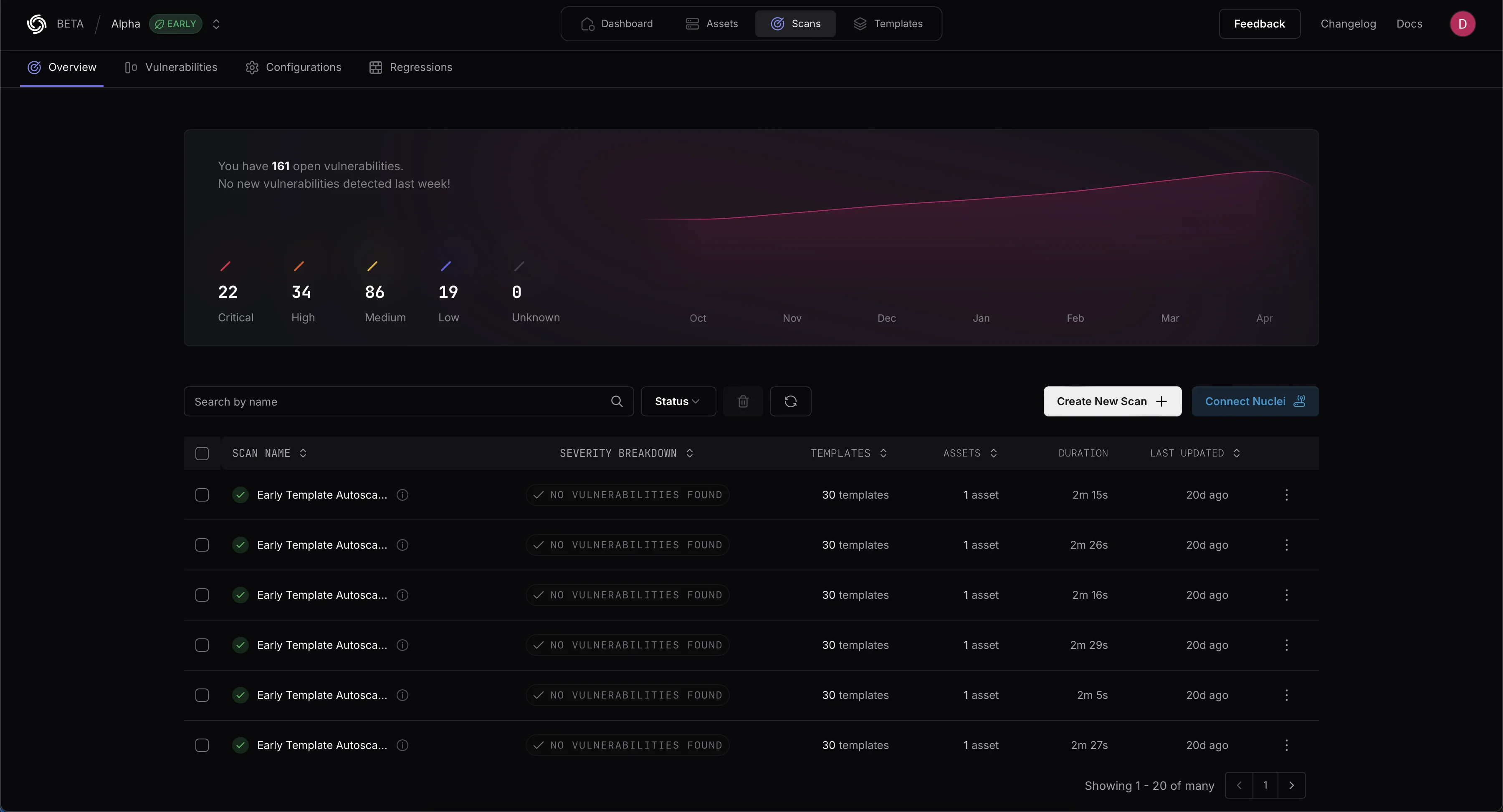
Where Nuclei falls short: Template coverage depends on the community — niche or proprietary API patterns may have no templates. Nuclei is not an interactive proxy; it handles authentication flows less gracefully than ZAP. False positive rates vary by template quality.
Best fit: Teams with a known API attack surface who want targeted testing of specific vulnerability classes. Nuclei shines for testing APIs at scale — many endpoints, many templates, automated. Pair with ZAP for broader coverage.
3. mitmproxy
mitmproxy is an open-source interactive HTTPS proxy for intercepting, inspecting, modifying, and replaying API traffic. It is the primary tool for manual API security testing: routing mobile app or web frontend API calls through mitmproxy reveals every endpoint the application calls, the exact request format, and the response structure.
What mitmproxy does well: Full TLS interception including certificate pinning bypass techniques. You can change user IDs in URLs, alter JWT claims, remove authentication headers, and inject special characters into request bodies at the byte level. Captured requests can be replayed with modifications for authorization testing, and a Python addon API enables automated request transformation.
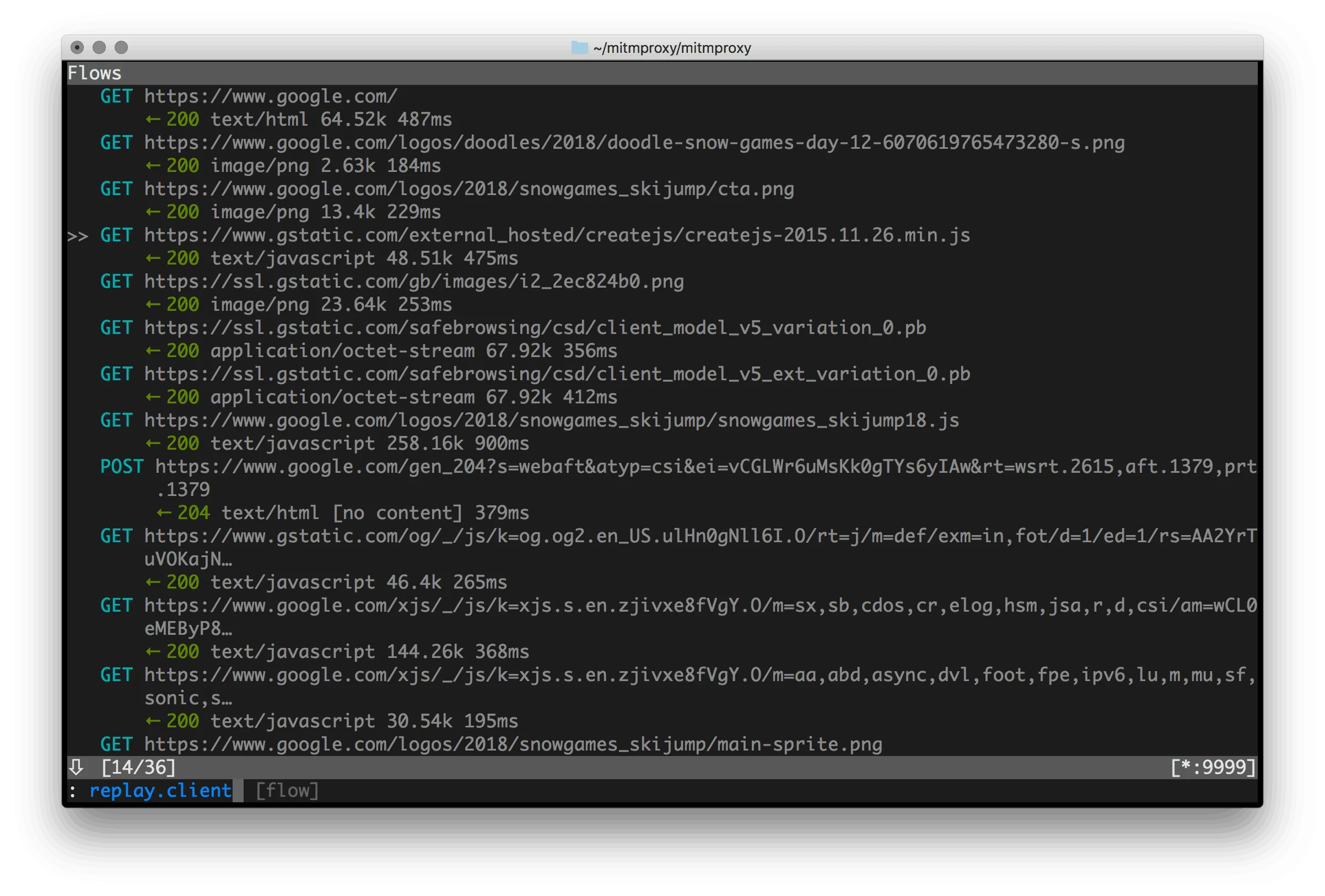
Where mitmproxy falls short: Manual tool — no automated vulnerability detection. Intercepting mobile apps with certificate pinning requires root access or emulation. No CI/CD integration in the traditional sense.
Best fit: Security engineers and penetration testers during manual API security assessments. mitmproxy is the primary tool for understanding undocumented API behavior and testing authorization boundaries. For mobile API security specifically, mitmproxy is standard in mobile app penetration testing workflows.
4. 42Crunch API Audit
42Crunch provides static analysis of OpenAPI 3.x specifications . The API Audit checks the API contract for security weaknesses before a single request is made: missing authentication definitions, overly permissive response schemas, lack of input validation rules, missing rate limiting, and OWASP API Top 10 coverage gaps in the spec.
What 42Crunch does well: Specification-level security analysis catches issues at the API design phase — before implementation even begins. The VS Code extension gives developers inline feedback as they write OpenAPI specs. CI/CD integration via GitHub Action or CLI scans the spec and fails the build when security issues are found. The scoring system (0-100) gives a consistent quality metric across API specs.
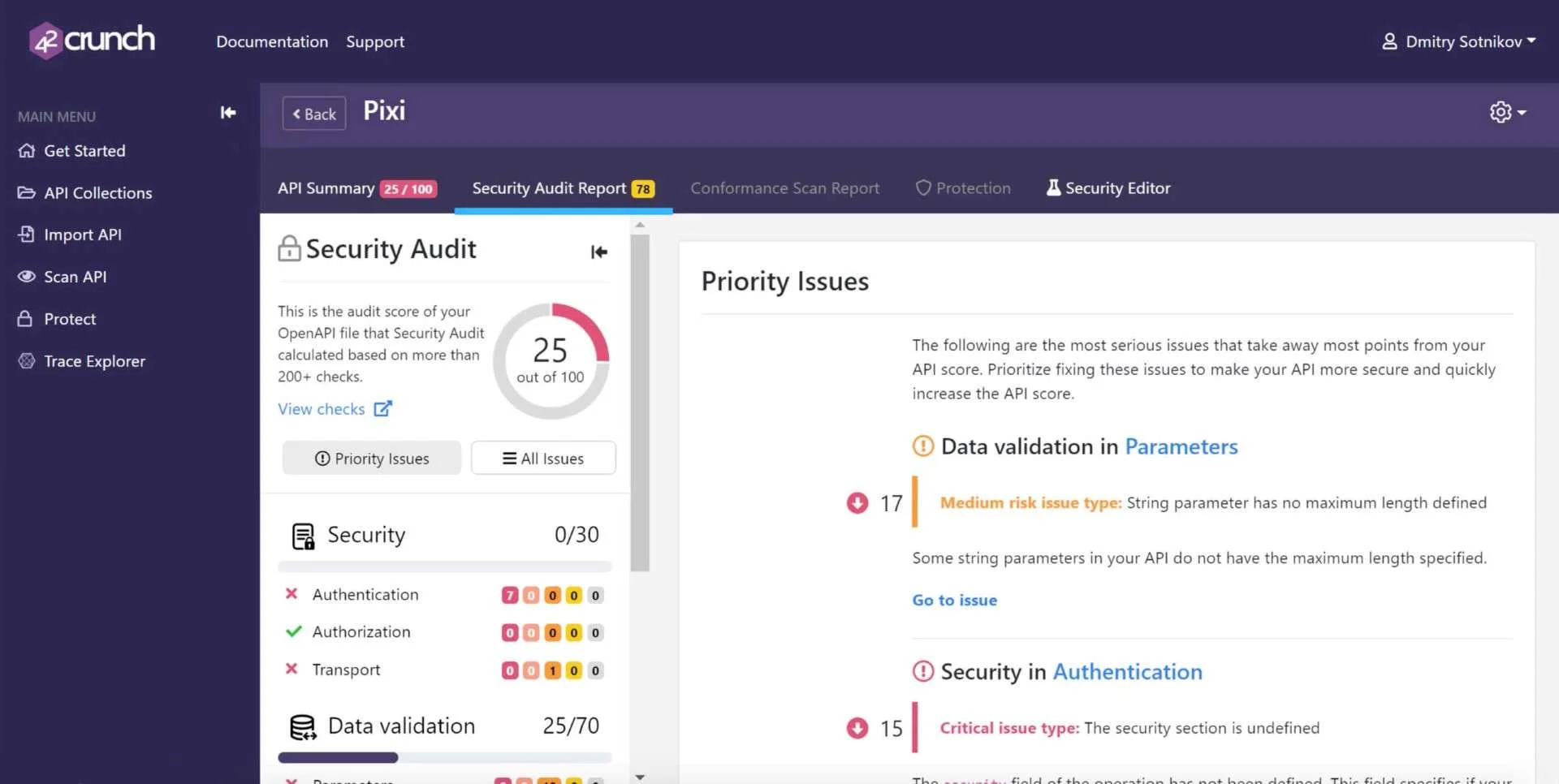
Where 42Crunch falls short: Static analysis only — it does not test a running API. A spec that passes 42Crunch Audit can still have runtime authorization bugs that only dynamic testing catches. The free tier limits some advanced features; penetration testing (Scan) requires paid access.
Best fit: Teams that maintain OpenAPI specifications. 42Crunch shifts API security left to the design phase — catching missing authentication or overpermissive schemas at spec time is cheaper than finding them in production. Pair with ZAP or Nuclei for dynamic testing coverage.
5. Escape
Escape is an API security scanner with a free tier that focuses on GraphQL and REST API security testing using AI-assisted fuzzing. It discovers APIs, generates test cases from the schema, and actively tests for OWASP API Top 10 vulnerabilities.
What Escape does well: Strong GraphQL support — GraphQL is poorly covered by most other open-source tools. Escape discovers the schema, generates mutation and query test cases, and tests for introspection exposure, query depth attacks, and authorization issues. The free tier allows scanning public endpoints. REST API scanning covers authentication weaknesses and common injection points.
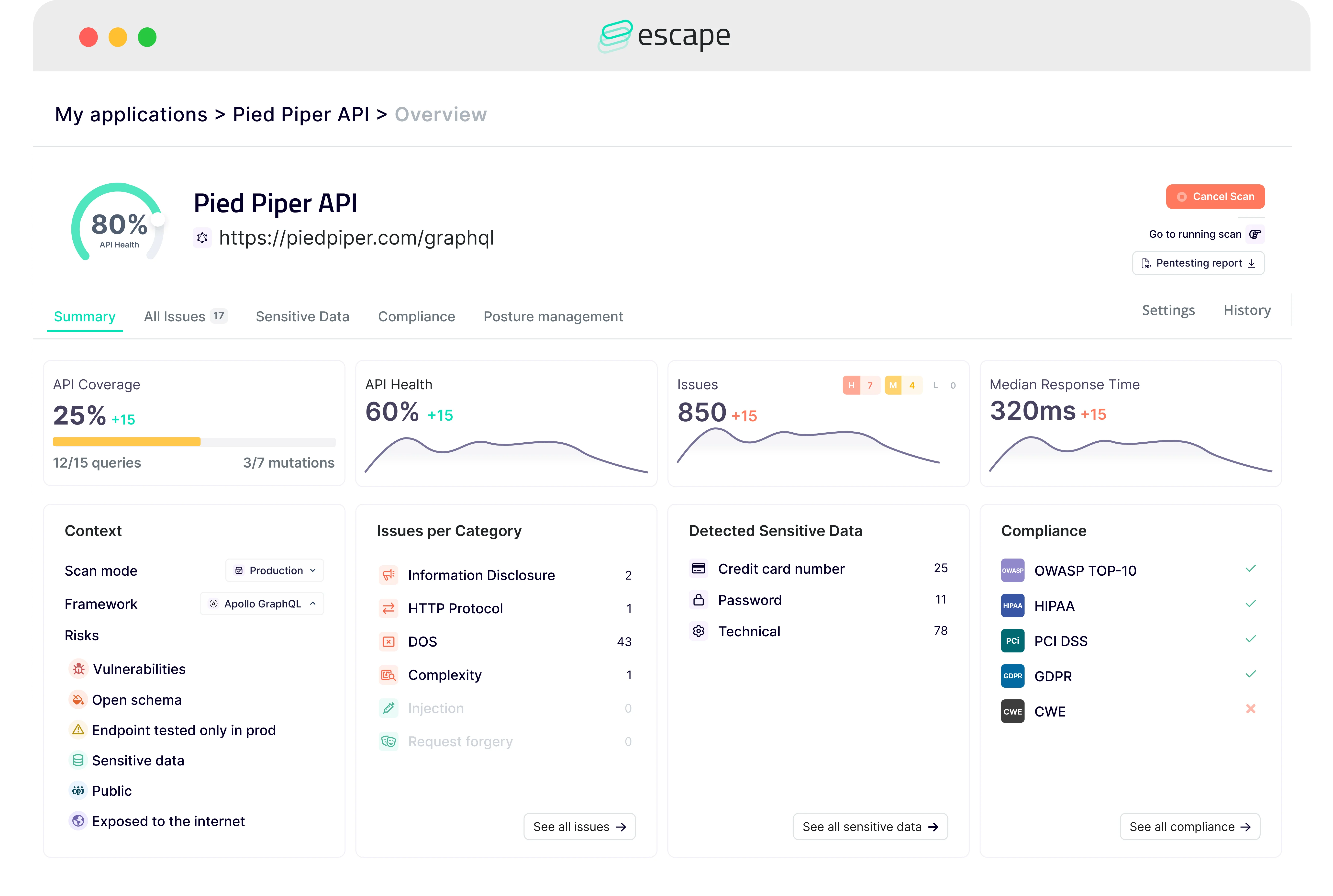
Where Escape falls short: The free tier is limited in scan depth and rate. The most capable features — CI/CD integration, comprehensive scanning, and team workflows — require a paid subscription.
Best fit: Teams with GraphQL APIs who need more than ZAP’s partial GraphQL support. Escape fills the GraphQL API security gap in the open-source tool landscape. See the broader API security tools category for commercial alternatives.
6. Bearer
Bearer is an open-source SAST tool that analyzes API source code for security vulnerabilities and data privacy issues. It detects hardcoded secrets in API handlers, missing authentication middleware, insecure data handling, SQL injection sinks in API routes, and exposure of PII in API responses or logs.
What Bearer does well: Source code level API security analysis — it understands framework routing patterns for Express, Rails, Django, and Spring, and can trace how data flows from API request parameters to database queries, external calls, and log outputs. OWASP API Top 10 mapping in findings. Free and open-source with no scan limits.
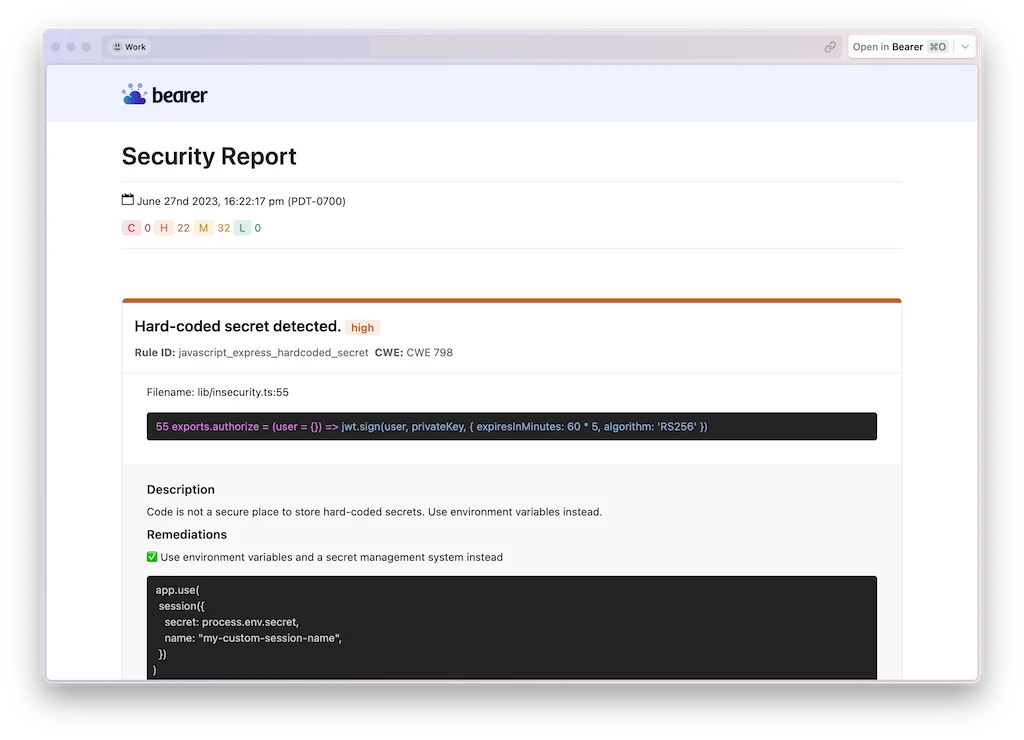
Where Bearer falls short: Static analysis only — it cannot detect runtime authorization issues like BOLA. Does not test a running API endpoint. Language support, while broad, may not cover every backend framework.
Best fit: Backend engineering teams that want API security feedback in CI before code is deployed. Bearer adds API security to code review without requiring a test environment. Complements dynamic testing tools that run against deployed APIs.
7. OWASP ZAP API Scan (GraphQL mode) and related OpenAPI scanners
Several lightweight OpenAPI security scanners complement ZAP and Nuclei for specific use cases: Schemathesis generates property-based test cases from OpenAPI specs and uses hypothesis testing to find edge cases that break APIs. RESTler (from Microsoft Research) is a stateful REST API fuzzer that chains API calls in logical sequences to reach states that simple scanners miss.
What these tools do well: Schemathesis finds edge cases in input validation that neither ZAP nor manual testing reliably catches — it generates thousands of inputs from the schema definition and tests how the API handles them. RESTler’s stateful fuzzing discovers authentication session management bugs and multi-step authorization flaws. Both are free and open-source.
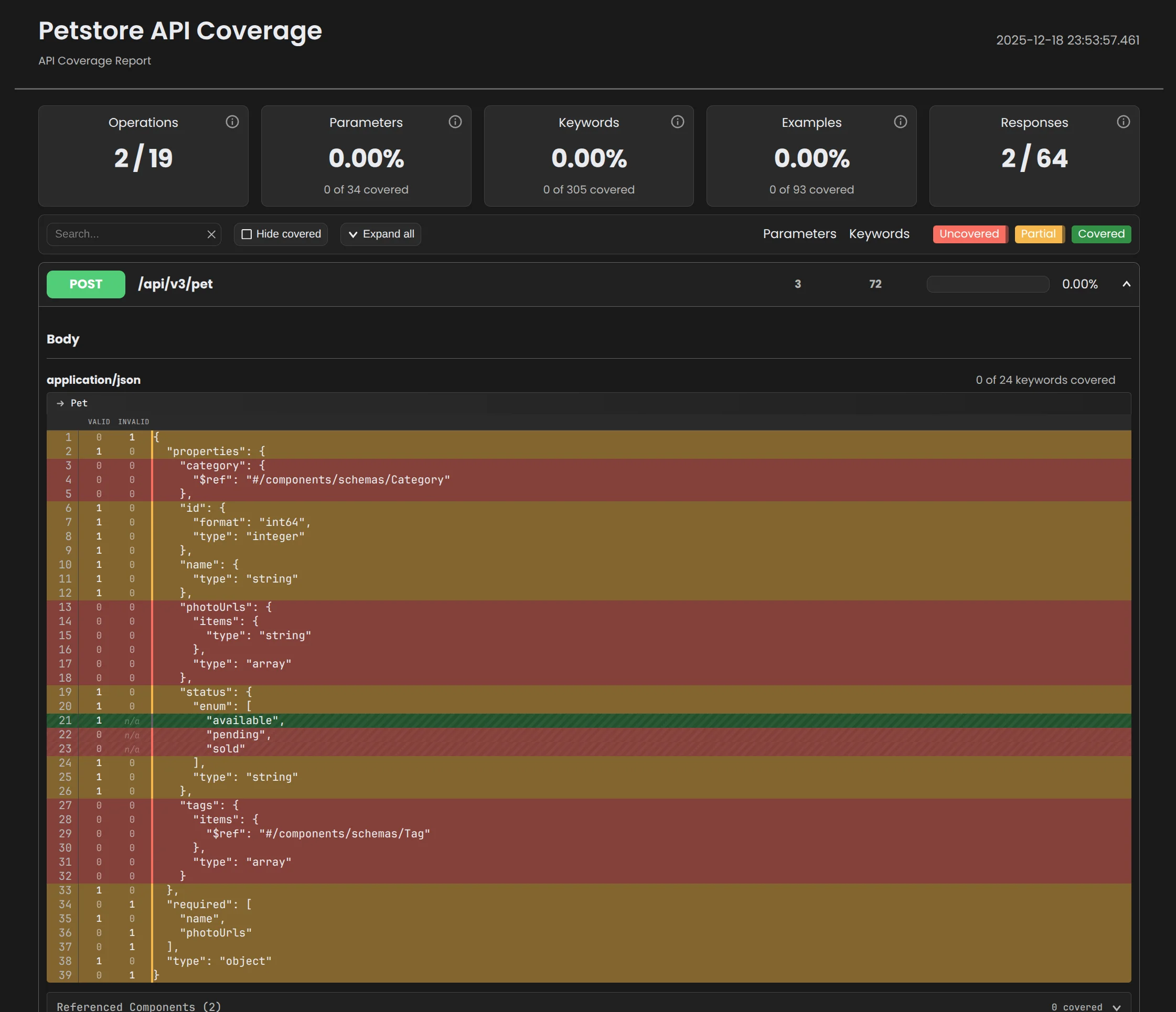
Where they fall short: Higher setup complexity than ZAP or Nuclei. RESTler requires a compiled binary and RESTler-specific configuration. Schemathesis works best when your OpenAPI spec is comprehensive and accurate.
Best fit: Teams that need comprehensive input validation testing (Schemathesis) or stateful multi-step API testing (RESTler) beyond what ZAP’s active scan covers.
Comparison table
| Tool | Type | REST | GraphQL | CI/CD | License |
|---|---|---|---|---|---|
| ZAP | DAST (active scan) | Yes (OpenAPI) | Partial | Yes | Apache 2.0 |
| Nuclei | Template scanner | Yes | Yes (templates) | Yes | MIT |
| mitmproxy | Proxy (manual) | Yes | Yes | No | MIT |
| 42Crunch | Static (spec analysis) | Yes (OpenAPI) | No | Yes | Free tier / Commercial |
| Escape | DAST (AI fuzzing) | Yes | Yes (strong) | Limited free | Free tier / Commercial |
| Bearer | SAST (source code) | Yes (code analysis) | Yes | Yes | Elastic License 2.0 |
| Schemathesis / RESTler | Fuzzing | Yes | No / Partial | Yes | Open source |
DAST vs static analysis for APIs
API security tools split into two categories based on what they analyze. Static analysis tools — 42Crunch and Bearer — examine code or specifications without running the API. Dynamic testing tools — ZAP, Nuclei, Escape — send real requests to a running API.
Neither alone is sufficient. Static analysis catches design flaws (missing authentication in the spec), implementation bugs (SQL injection in the code), and privacy issues (PII logged) before deployment. Dynamic testing finds runtime authorization bugs that cannot be seen in static code: BOLA, where user A can access user B’s resources, only manifests when you actually try the unauthorized request.
A complete API security posture requires both: Bearer or 42Crunch in the PR check, ZAP or Nuclei in the integration test environment. See what is API security for a broader framework on API security coverage.
CI/CD integration
ZAP API scan in GitHub Actions:
- name: ZAP API scan
uses: zaproxy/action-api-scan@v0.7.0
with:
target: "https://api.example.com/openapi.json"
fail_action: true
Nuclei targeted API scan:
nuclei -l api-endpoints.txt -t nuclei-templates/exposures/apis/ -severity high,critical
Bearer source scan:
bearer scan ./src --severity=high --exit-code 1
42Crunch in CI:
42c-ast audit --fail-on-error --input openapi.yaml
For a complete DevSecOps pipeline with API security gates, see the DevSecOps tools guide and DevSecOps implementation guide .
How to choose
Starting from scratch: Add 42Crunch API Audit to your OpenAPI spec linting step, run ZAP API scan against your test environment in CI, and use mitmproxy for manual exploratory testing during development. That covers design, implementation, and integration testing.
GraphQL API: Escape is the most capable free option for GraphQL-specific security testing. Nuclei templates add GraphQL introspection and injection checks. ZAP’s GraphQL coverage is improving but still partial.
Security-focused CI/CD: Bearer in the code review stage catches source-level API security issues before they reach a test environment. Pair with Nuclei for template-based checks against the deployed test API.
Penetration testing: mitmproxy for traffic interception, Nuclei for targeted exploit templates, and ZAP in manual mode for interactive testing cover the standard API penetration test toolkit.
For commercial API security platforms that add continuous monitoring and API discovery, see the full API security tools list.






