9 Best API Security Tools (2026)
Independent ranking — no vendor pays to appear here. See methodology.
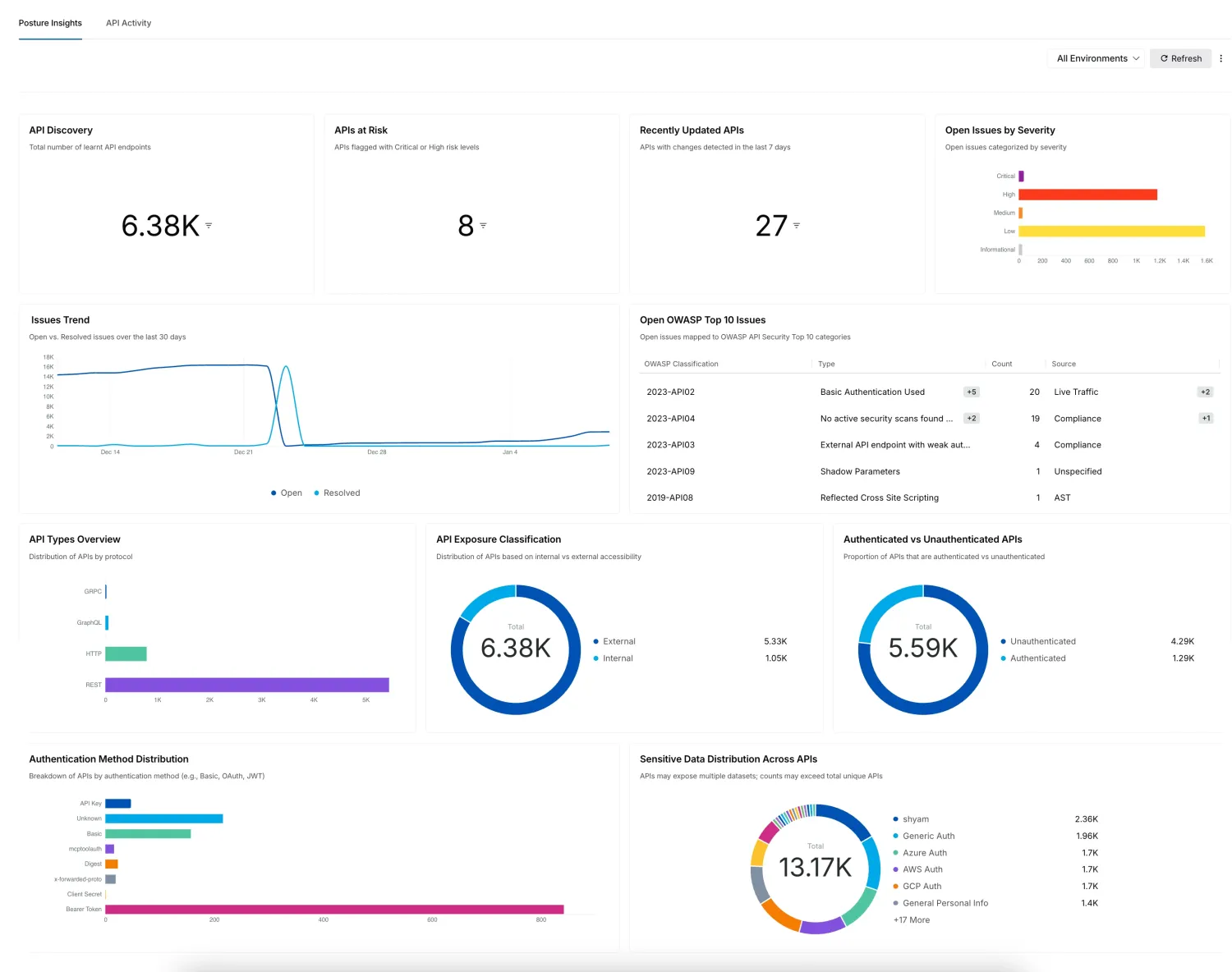
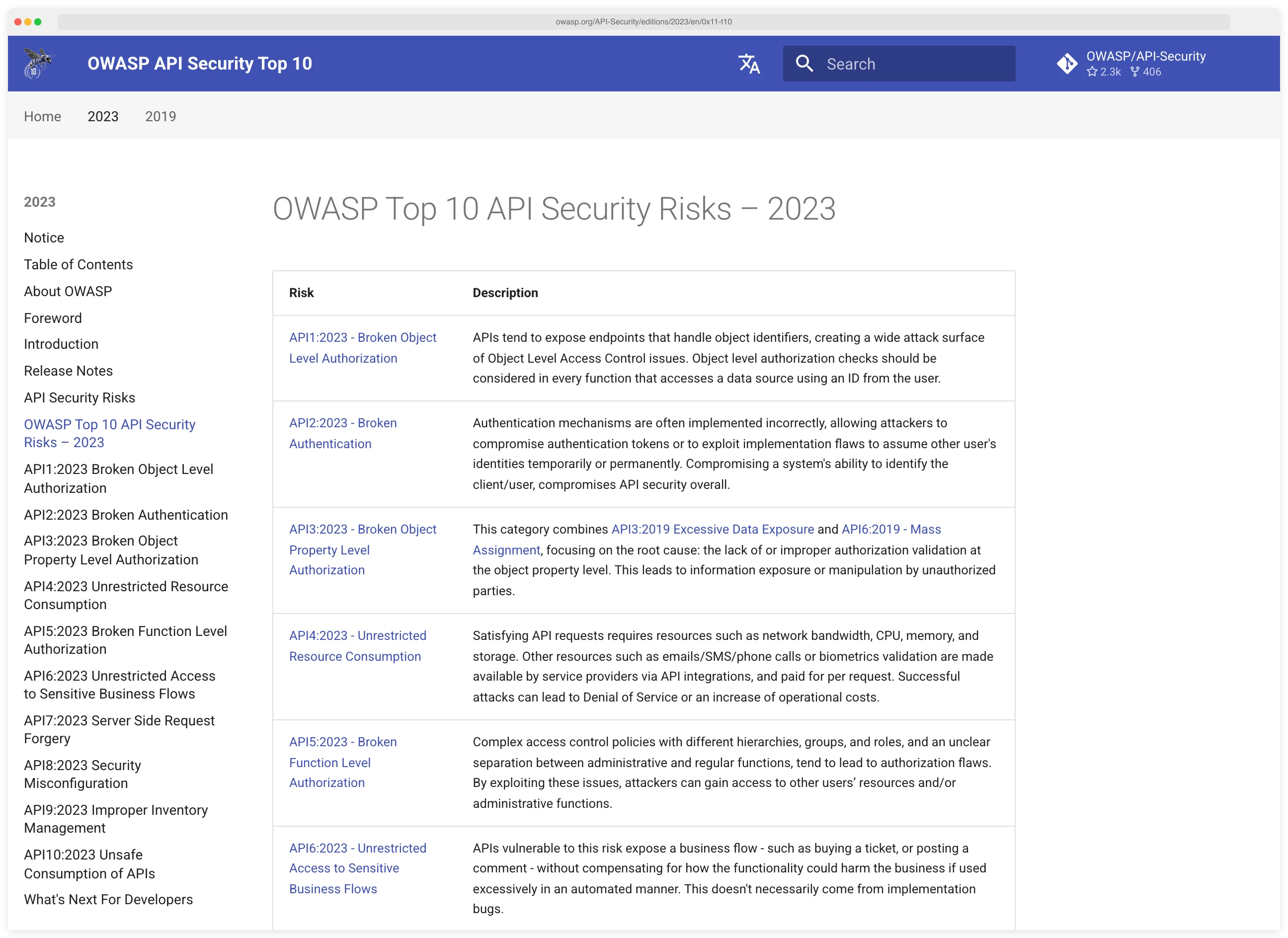
Compare 5+ API security tools for 2026. Shadow API discovery, OWASP API Top 10 testing, and protection against BOLA and authentication bypass.
At a glance
The best API security tools in 2026: Salt Security, Wallarm, 42Crunch, Cequence, and Akamai API Security (formerly Noname).
- Best runtime API security platform: Salt Security — strongest behavior-based BOLA + auth-bypass detection
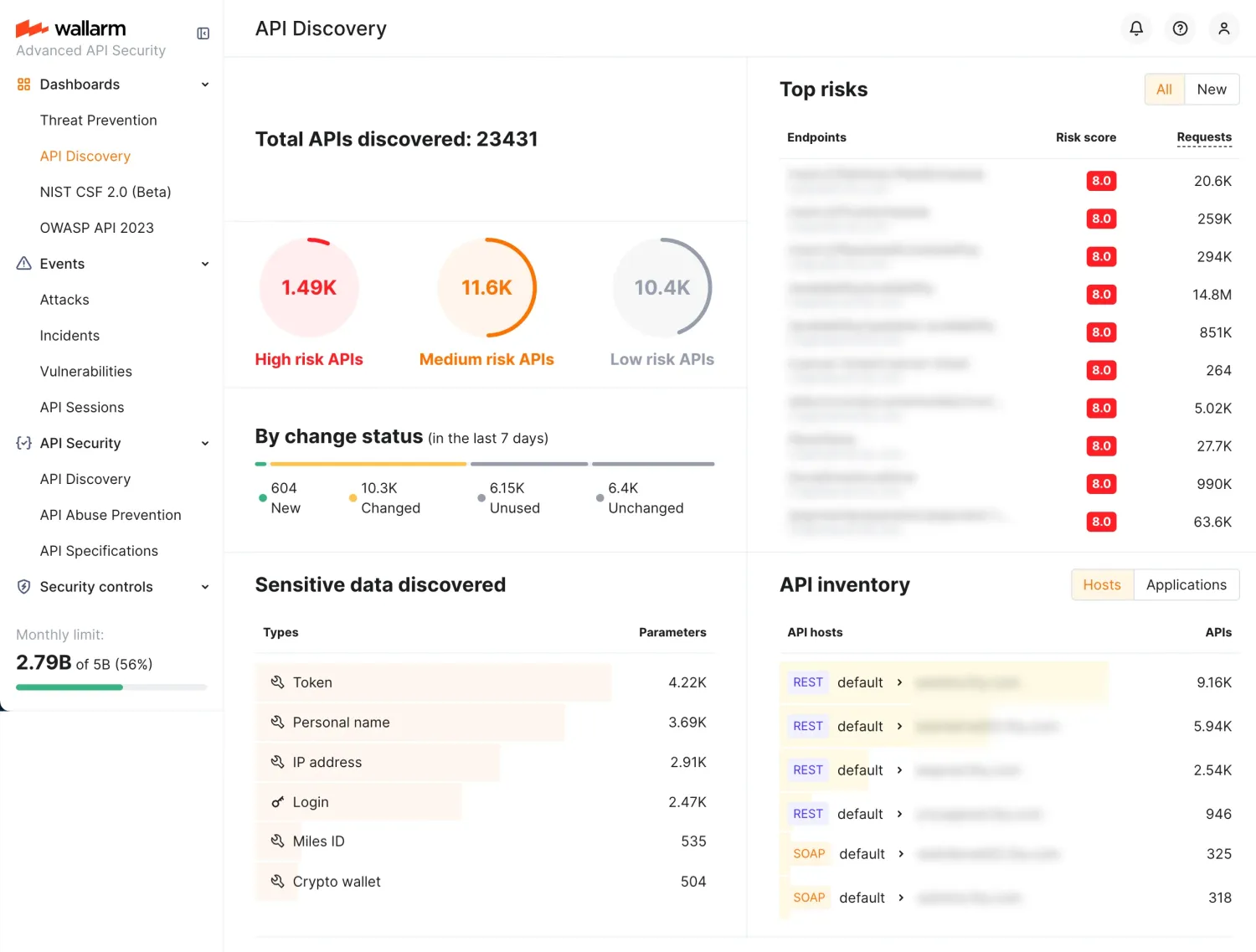
- Best for shift-left + WAAP combo: Wallarm — unified API security across discovery, testing, and runtime
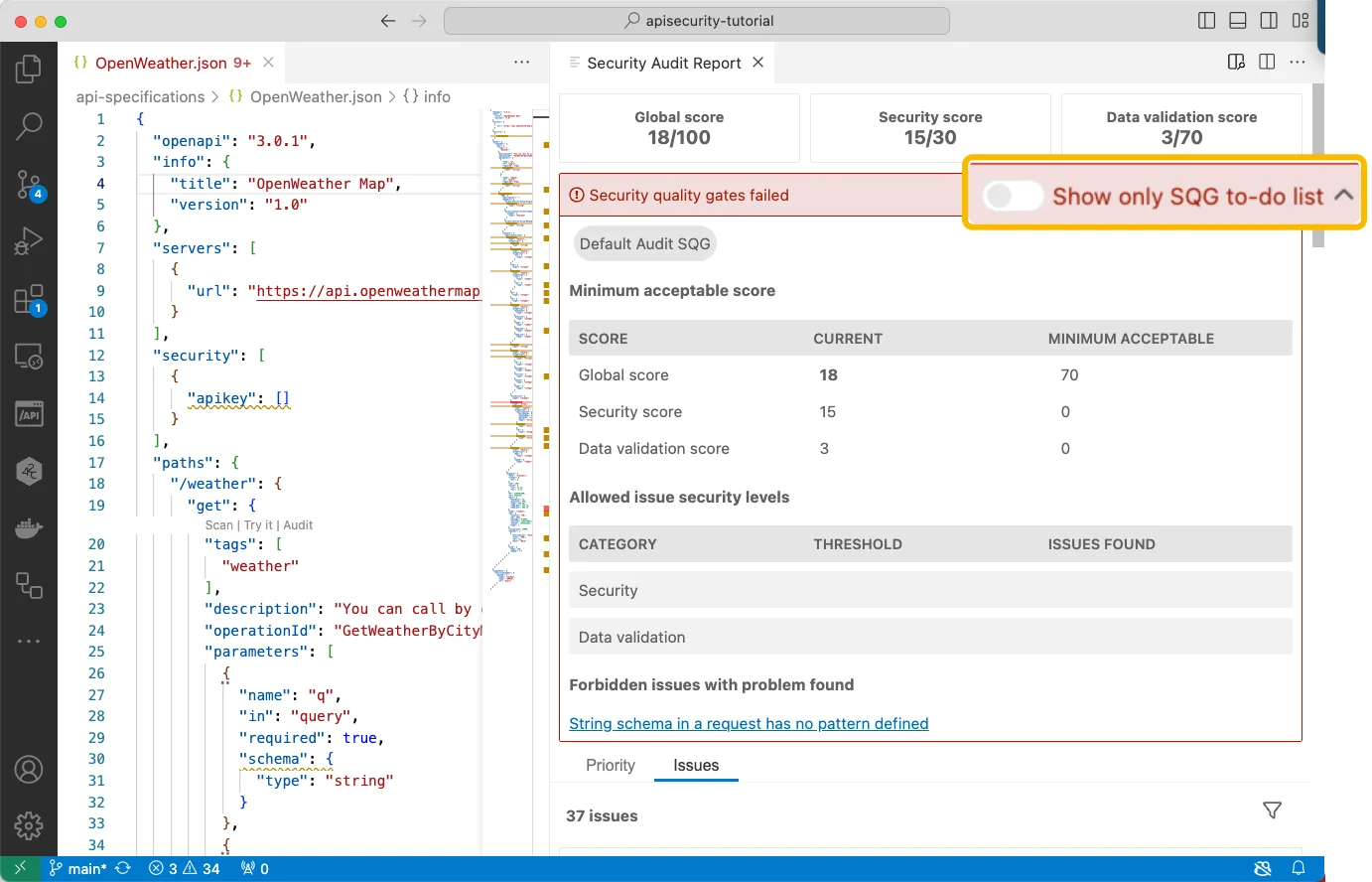
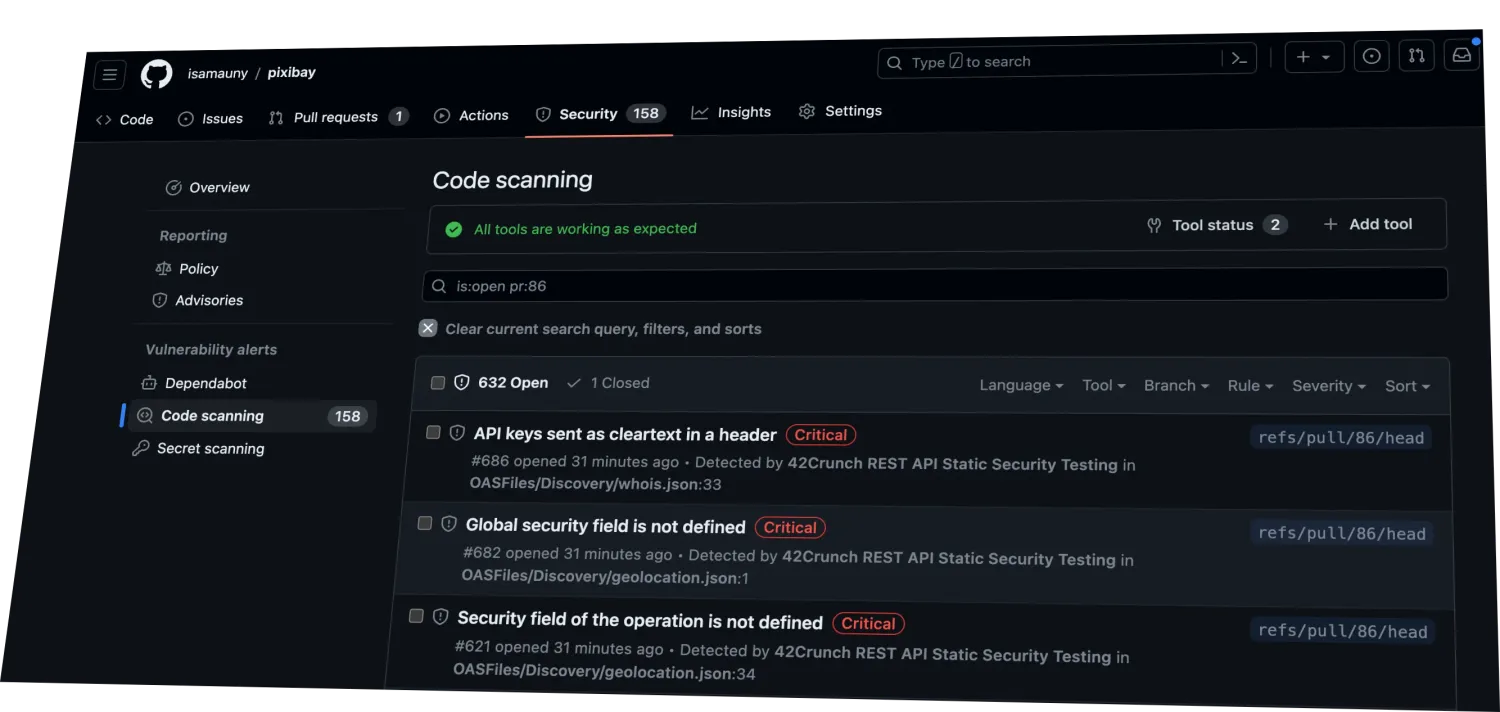
- Best for spec-driven API testing: 42Crunch — deep OpenAPI contract validation in CI/CD
- Best for bot + API abuse defense: Cequence — strongest credential-stuffing and scraping defense
- Best enterprise API discovery: Akamai API Security (formerly Noname) — broadest agentless discovery across cloud + on-prem
I evaluated API security platforms across shadow-API discovery, OWASP API Top 10 coverage, runtime protection, and CI/CD shift-left testing — using vendor docs, OWASP API Security Project research, and Gartner API security analysis. No vendor paid to appear on this page.
Best API Security Tools in 2026
The best API security tools in 2026 are Akto, 42Crunch, Salt Security, Akamai API Security, and APIsec.
Akto is the strongest free option open-source with 1,000+ security tests and an active community
And the only API security tool with no fully-free commercial competitor at parity. 42Crunch leads on OpenAPI spec auditing and contract conformance testing, making it the right pick for teams that design APIs before building them.
Salt Security leads the runtime protection tier with inline traffic inspection and ML-based behavioral threat detection across production API traffic. Akamai API Security (acquired from Noname Security in June 2024) adds full API lifecycle protection from discovery through runtime to compliance.
APIsec is an AI-powered API pentesting option with a free tier for smaller API portfolios.
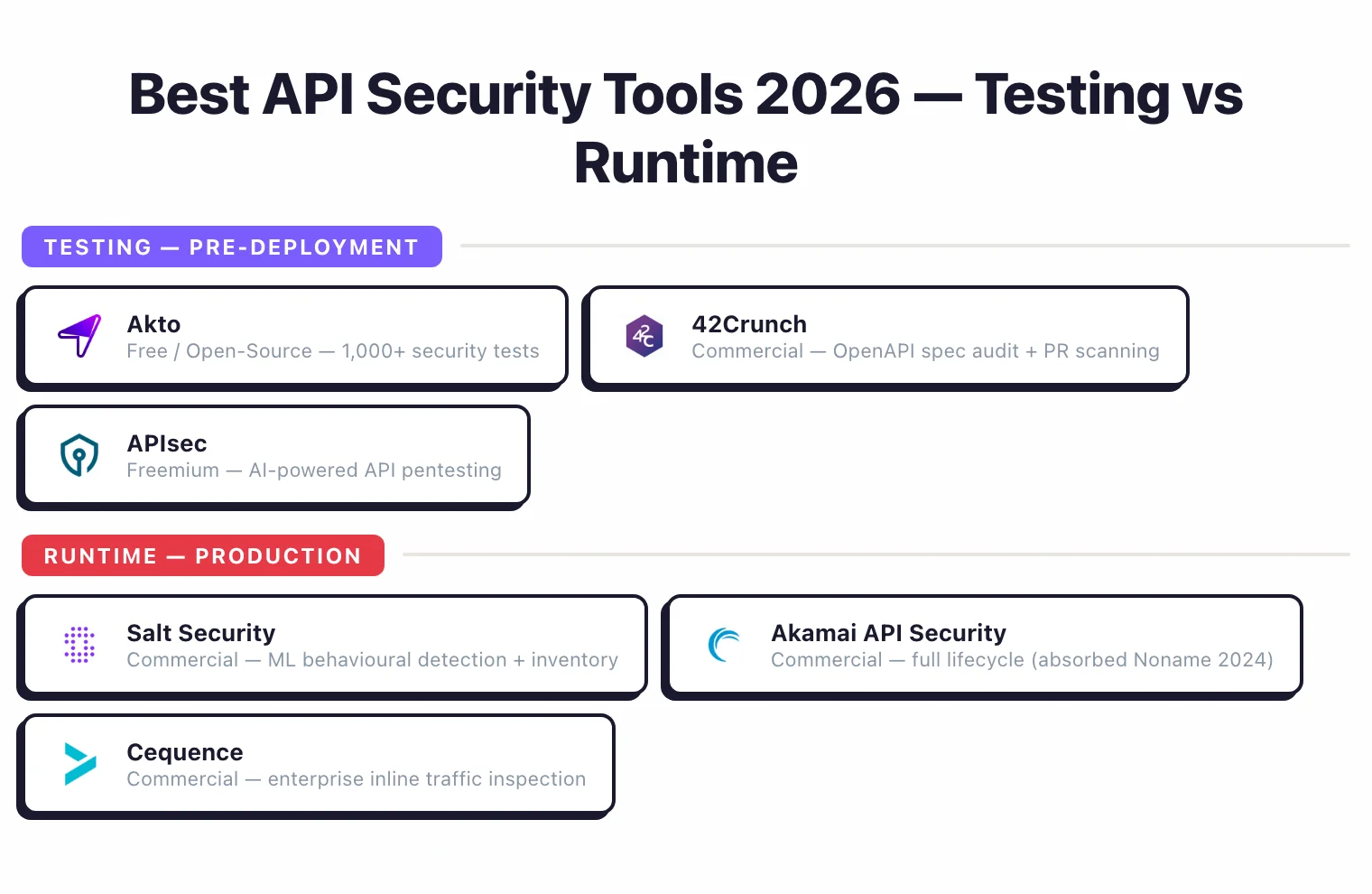
For teams choosing between testing tools and runtime protection: testing tools (42Crunch, APIsec, Akto) fit pre-deployment security gates; runtime tools (Salt, Akamai, Cequence) fit production anomaly detection. No vendor pays to appear here — rankings are based on publicly verifiable evidence.
AppSec Santa is vendor-neutral. No tool vendor on this page pays to be included, ranked higher, or excluded from comparisons.
Each tool is evaluated against the same criteria applied across all API security reviews on this site: OWASP API Top 10 coverage, API discovery capability, runtime protection depth, CI/CD integration, and pricing transparency.
The testing-versus-runtime distinction is central to this category — a testing tool and a runtime protection tool are not interchangeable, and this comparison treats them separately. Where vendor claims about detection rates or API coverage cannot be independently verified, I note that explicitly.
What is API Security?
API security is the practice of protecting application programming interfaces from vulnerabilities and attacks throughout their lifecycle — from design and development through production deployment. It sits inside the broader application security discipline as the layer focused on API-specific risk.
While DAST tools can test APIs to a point, dedicated API security tools dig deeper into broken authentication, excessive data exposure, rate limiting gaps, and business logic flaws that generic scanners miss.
The threat is growing fast. Salt Security’s Q1 2025 State of API Security Report found that 34% of organizations reported sensitive data exposure as an API security issue in the past 12 months, while only 10% had any API posture governance strategy in place.
Wallarm’s Q3 2025 API ThreatStats Report counted 1,602 API vulnerabilities in that quarter alone, up 20% from Q2.
These figures reflect how APIs have become the primary attack surface for modern applications, yet most organizations lack adequate protections.
API security tools split into two camps: testing tools like 42Crunch and APIsec that scan before deployment, and runtime protection tools like Salt Security and Cequence that monitor production traffic for anomalies and active attacks.
Quick Comparison of API Security Tools
| Tool | USP | Type | License |
|---|---|---|---|
| Freemium | |||
| APIsec | AI-powered API pentesting platform | Testing | Freemium |
| Commercial | |||
| 42Crunch | OpenAPI spec audit & conformance | Testing | Commercial |
| Akamai API Security | Full API lifecycle protection (from Noname acquisition) | Both | Commercial |
| Cequence Security | API security + bot management | Runtime | Commercial |
| Imperva API Security | ML-driven API discovery and runtime protection, part of Thales | Both | Commercial |
| Levo.ai NEW | eBPF-powered API discovery + LLM security | Discovery + Testing | Commercial |
| Salt Security | AI/ML-powered API discovery | Runtime | Commercial |
| Wallarm | Integrated WAF + API protection | Runtime | Commercial |
| Acquired (2) | |||
| Noname Security ACQUIRED | Acquired by Akamai (June 2024); now Akamai API Security | Was Runtime | Was Commercial |
| Traceable AI ACQUIRED | Merged with Harness (March 2025); API security now part of Harness DevSecOps platform | Was Both | Was Commercial |
Top 5 API Security vendors compared in detail
The five vendors below are the ones most frequently cited when buyers compare API security platforms. Each profile lists buyer fit, two or three documented strengths, and limitations sourced from public G2 and Gartner Peer Insights reviews.
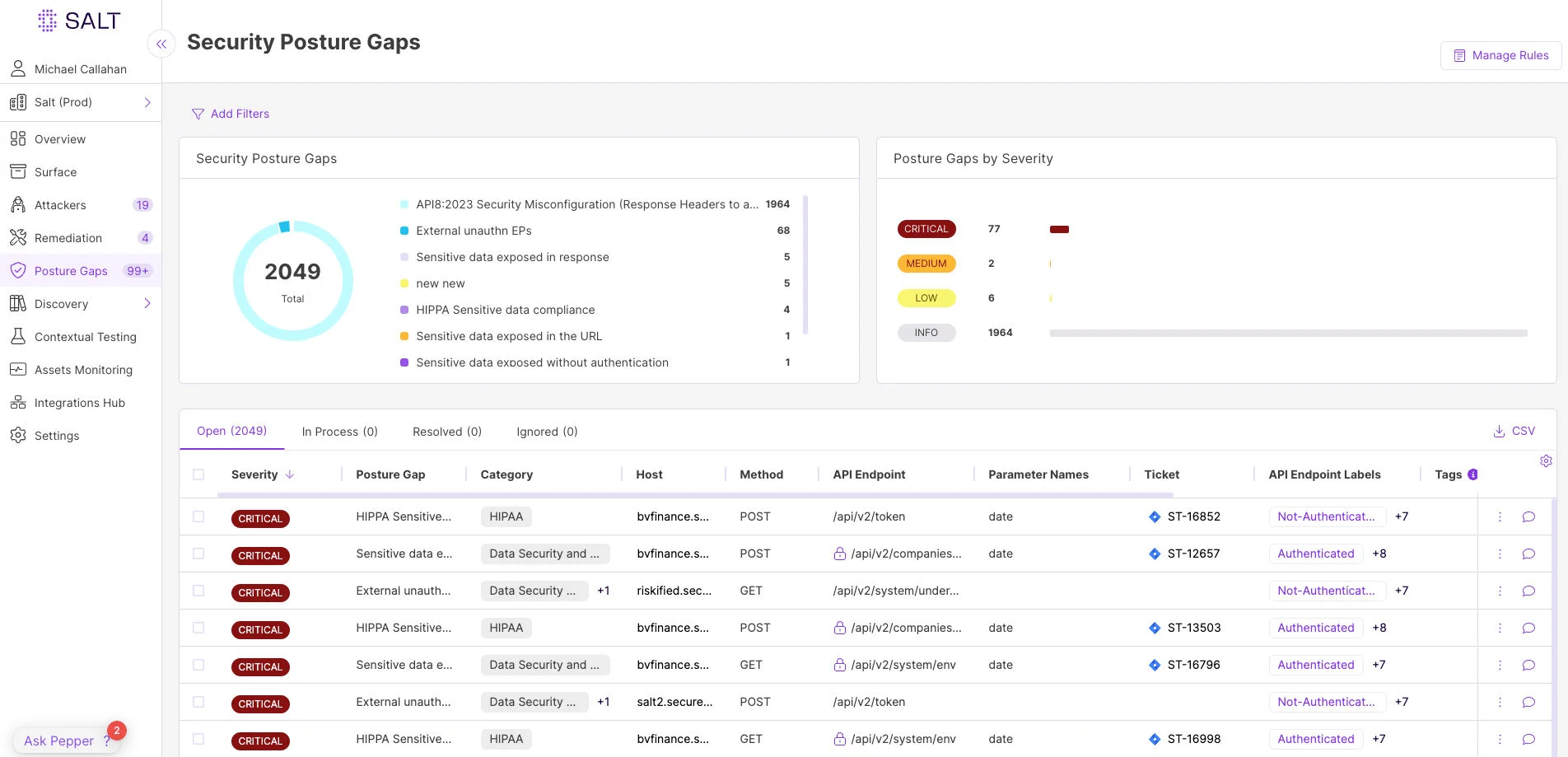
Salt Security
Best for: Teams running externally consumed APIs that need behavioural anomaly detection plus inventory in one platform.
- Strengths: Continuous API discovery with behavioural baselines per consumer. Strong tenant-aware analytics for BOLA-class detection. Pivoted to lead with agentic AI and MCP discovery in 2026 product positioning.
- Watch out for (per public G2 reviews): Pricing transparency is limited; quotes are size-dependent. Initial baseline learning runway is several weeks before signal stabilises.
Akamai API Security
Best for: Existing Akamai CDN/WAF customers who want a single edge-plus-API control plane.
- Strengths: Absorbed Noname Security in 2024, pairing API discovery and runtime protection with Akamai’s CDN+WAF. One vendor for edge, perimeter, and API-layer policy. Strong public-API protection at internet scale.
- Watch out for (per public G2 reviews): Migration from standalone Noname tooling has been uneven for some customers. Best fit when CDN sits with Akamai already; less compelling as a standalone API security buy.
Traceable AI
Best for: DevSecOps teams already on Harness who want API security inside the same delivery platform.
- Strengths: Distributed tracing model surfaces full request lineage across microservices. Strong on east-west API visibility via service-mesh integration. Now bundled with Harness DevSecOps for unified pipeline policy.
- Watch out for (per public G2 reviews): Integration depth varies by language runtime. Post-Harness merger, roadmap clarity for the standalone Traceable product is still settling.
Wallarm
Best for: Teams that want API security plus WAAP coverage in one platform without a CDN dependency.
- Strengths: Combined API security and WAAP via single agent. Self-hosted and SaaS deployment options. eBPF-based runtime monitoring for east-west traffic in Kubernetes.
- Watch out for (per public G2 reviews): Dashboard customisation is limited compared to enterprise leaders. Documentation depth lags Salt and Akamai for advanced policy authoring.
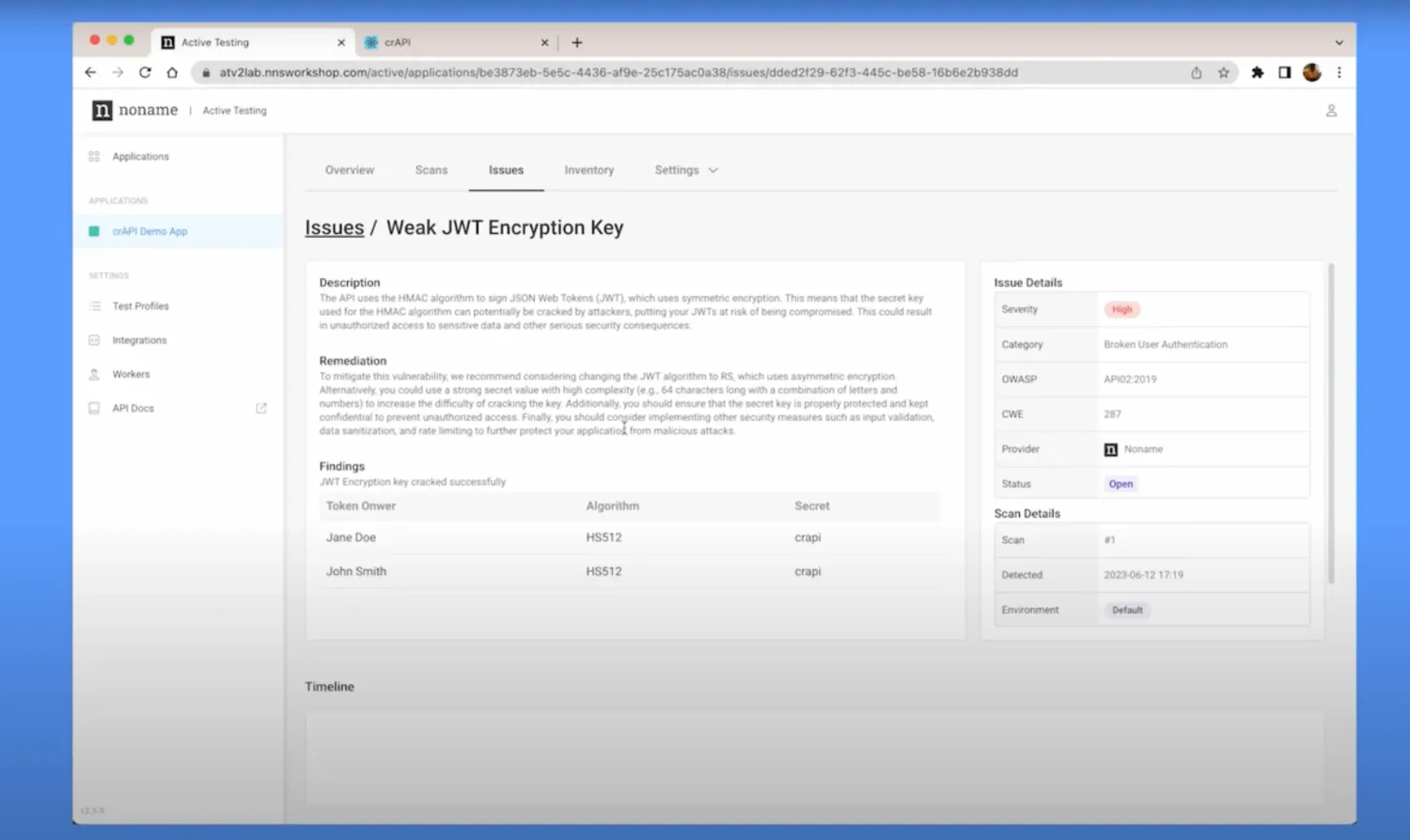
42Crunch
Best for: Teams with mature OpenAPI specifications that want shift-left API testing in PR review.
- Strengths: Spec-driven security audit catches contract issues before merge. Integrates with VS Code, GitHub, and major CI platforms. Strong on OpenAPI conformance and authorization-flaw static analysis.
- Watch out for (per public G2 reviews): Value drops sharply when OpenAPI specs are missing or stale. Runtime protection is not a primary capability — pair with Salt or Akamai for production.
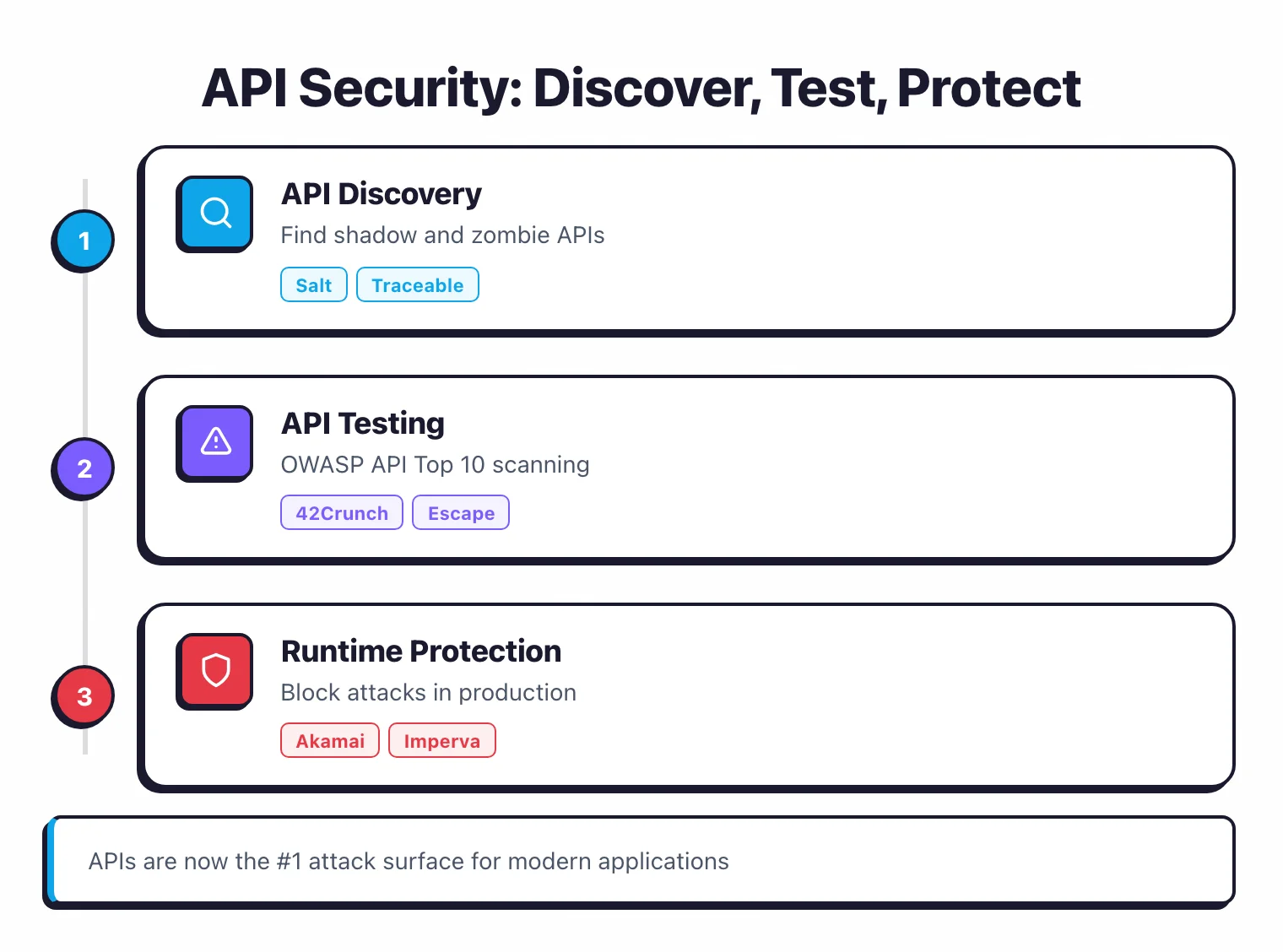
What is the Difference Between API Testing and Runtime Protection?
Similar to AI security , API security tools break into two groups. API testing tools audit your API specifications and endpoints before deployment to catch design flaws early.
Runtime protection tools sit in front of production APIs to detect and block attacks in real time.
| Aspect | API Testing | API Runtime Protection |
|---|---|---|
| When it runs | Before deployment | In production |
| Purpose | Find vulnerabilities in API design | Block attacks, detect anomalies |
| Examples | 42Crunch, APIsec, Levo.ai | Salt Security, Cequence, Wallarm |
| Input needed | OpenAPI specs, traffic samples | Live traffic |
| Best for | Development and QA | Production monitoring |
My take: Most teams should start with API testing in CI/CD to catch broken authentication and authorization issues before they ship. Layer on runtime protection for any production APIs that handle sensitive data or face the public internet — that combination of shift-left testing and runtime monitoring covers the full API lifecycle.
How is the API Security Market Changing?
The API security market is consolidating rapidly. Since mid-2024, major acquisitions and strategic pivots have reshaped the competitive landscape:
Noname Security → Akamai (2024)
Akamai picked up Noname Security in June 2024 for roughly $450M. Akamai API Security now rolls both platforms together for API discovery, testing, and runtime protection.
Akto Pivots to AI Agent Security
Akto, one of the most widely adopted open-source API security testing tools, shifted focus from API security to AI agent and MCP security in 2025. The original open-source API security tool still works, but the company's attention is on agentic security now.
Market Leaders
The 2025 KuppingerCole Leadership Compass for API Security and Management named 15 Overall Leaders, including Cequence Security, Salt Security, Akamai API Security, 42Crunch, and Wallarm.
Traceable AI → Harness (2025)
Traceable AI merged with Harness in March 2025. Both companies were founded by Jyoti Bansal, so the merger was probably inevitable.
What’s Next for API Security in 2026 and Beyond
The API security mandate is widening. Four trends are reshaping the category through 2026 and into 2027.
GenAI and MCP server attack surface
API security is no longer just REST and GraphQL. LLM endpoints, agent tool-calls, and Model Context Protocol (MCP) servers are now first-class API surfaces with their own threat model.
Salt Security now leads its homepage with “Agentic AI Security, MCP Discovery, and API security” — a positioning shift that mirrors where the rest of the category is heading. Prompt-injection-as-API-attack and tool-call abuse are the new top entries on internal threat lists.
Discovery tooling has to map agentic endpoints, not just human-facing routes. Existing SAST and runtime stacks largely miss this surface today.
Behavioural detection beyond OWASP API Top 10
Static rule sets stop at known classes. Runtime traffic learning, anomaly scoring, and intent classification are the next layer.
Salt Security , Akamai API Security , and Wallarm all market behavioural baselines that flag deviations a rule engine cannot pre-encode. The trade-off is the 4-8 week learning runway plus tenant-specific tuning before signal beats noise.
The realistic 2026 expectation: behavioural detection complements OWASP rules, not replaces them.
Single control plane vs four overlapping stacks
The four-stack pattern (gateway + CDN/WAF + dedicated API security + service mesh) is buckling under operational load. Consolidation is well underway.
Akamai merged Noname into its CDN+WAF in 2024 and now sells a single API-security-plus-edge bundle. Expect Cloudflare and Fastly to follow with native API security in their WAF tier within 12-18 months.
The buyer-side question shifts from “which API security tool” to “which CDN do I already pay for, and does its API security tier suffice”.
Shift-left OpenAPI fuzzing in PR
Design-time API testing is moving into pull-request review, not just nightly CI.
42Crunch and StackHawk are pushing OpenAPI-spec-driven fuzzing into the PR layer, so a contract change that breaks an authorization invariant fails the review before merge. This compresses the fix loop from days to minutes.
The 2027 watch item: agentic remediation across the OWASP API Top 10. Several vendors are quietly piloting AI fix suggestions for BOLA and BOPLA findings; the question is whether those suggestions hold up under tenant-isolation review.
Drawbacks and Limitations of API Security Tools
API security tooling has matured fast, but the category still has structural blind spots. Three drawbacks come up repeatedly in buyer feedback.
East-west and internal API visibility gaps
Most commercial tools sit at the gateway, the CDN edge, or in front of the load balancer. That captures north-south traffic between clients and your perimeter, but service-to-service calls inside the cluster never cross those choke points.
A microservice-heavy SaaS often handles several times more east-west traffic than north-south, and a BOLA exploit between two internal services is invisible to a gateway-anchored scanner.
The realistic mitigations are service-mesh integration (Wallarm , Salt Security ) or eBPF-based runtime instrumentation. Both add operational complexity that vendor marketing rarely flags upfront.
BOLA and BOPLA false-positive density
Authorization-flaw detection is the hardest primitive in API security. The OWASP API Top 10 puts BOLA at #1 and BOPLA at #3 because they require understanding tenant boundaries and object ownership, not just request shape.
False-positive density on these classes is high in untuned deployments, and SOC queues routinely fill with authorization noise for weeks before suppression rules stabilise.
The result is alert fatigue: real BOLA incidents get muted alongside the noise. Plan for a 4-8 week tuning runway and a security engineer who owns the suppression policy, not just the tool.
Integration tax across overlapping stacks
Most enterprises end up running four overlapping control planes: an API gateway (Kong, Apigee, AWS API Gateway), a CDN with WAF (Cloudflare, Akamai, Fastly), a dedicated API security tool, and an internal service mesh.
Each stack has its own integration surface, its own policy language, and its own incident response loop. Consolidating to one vendor (Akamai’s API Security + WAF + CDN bundle is the leading example) reduces tax but locks pricing power to a single supplier.
For teams smaller than ~50 engineers and APIs with single-digit external consumers, dedicated API security tooling is often overkill — gateway-level rate limiting, OAuth scopes, and a quarterly OWASP API Top 10 manual test cover the realistic threat model.
Who Needs API Security Tools? Common Use Cases
API security tools are not a universal control. The buyer fit is shaped by who consumes the API and which trust boundary it crosses. Three patterns dominate.
Public API providers
If your APIs are externally consumed (Stripe, Twilio, Slack, GitHub-shaped platforms), they are a primary attack surface — not a secondary one.
Public APIs face credential stuffing, scraping, BOLA via guessable IDs, and abuse via leaked tokens. OWASP API Top 10 testing is mandatory at this scale, and runtime traffic monitoring catches what design-time testing misses.
Best fit: design-time testing (42Crunch , APIsec ) plus runtime protection (Salt Security , Akamai API Security ). The signal you are in this bucket: any external rate-limit incident or scraping complaint in the last 12 months.
Multi-tenant SaaS platforms
In a multi-tenant SaaS, tenant-isolation bugs are the dominant API risk class. BOLA and BOPLA flaws let one customer read or modify another customer’s data through a legitimate API call with a manipulated object identifier.
Static analysis catches some of this, but the only realistic catch-all is runtime detection that learns each tenant’s normal access pattern and flags anomalies.
Best fit: runtime API security with tenant-aware behavioural analytics (Salt Security , Wallarm , Traceable AI ). Signal you are in this bucket: any past or near-miss IDOR/BOLA finding from a pen test or bug bounty.
B2B partner integrations
When partners consume your APIs with long-lived credentials, the threat shifts from your own auth code to your partners’ security posture. A compromised partner credential becomes your incident.
API gateways enforce request shape and rate limits but cannot tell a legitimate partner request from a stolen-credential request that uses the same client ID. Behavioural baselines and credential-rotation enforcement are needed instead.
Best fit: API security with credential-anomaly detection plus a hard rotation policy on partner tokens (Akamai API Security , Cequence ). Signal you are in this bucket: any partner integration older than 12 months without forced credential rotation.
How Do I Choose the Right API Security Tool?
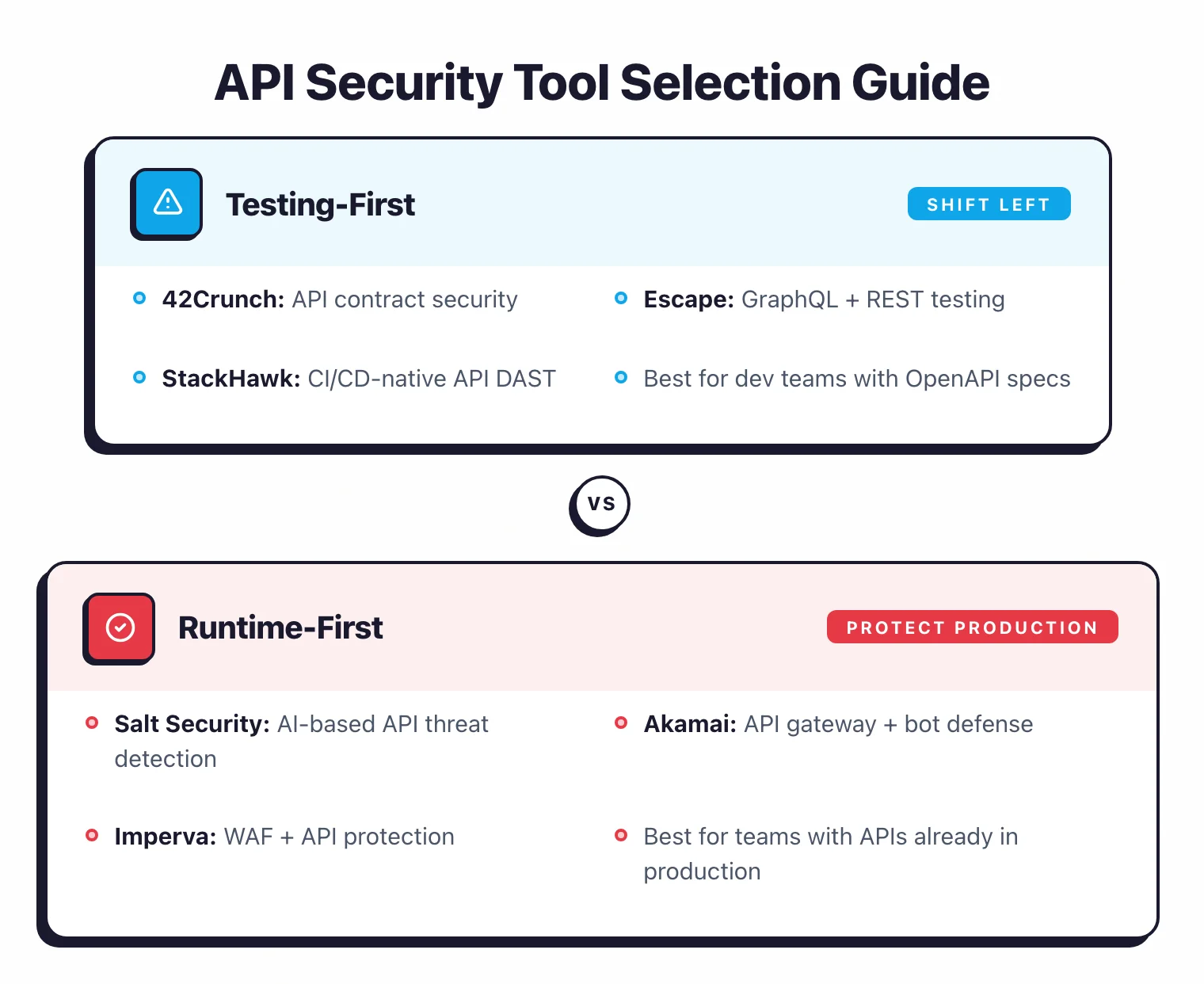
Testing vs Runtime Protection
Need to catch issues before deployment? Start with 42Crunch or APIsec. Need to spot attacks in production? Look at Salt Security, Cequence, or Wallarm.
API Discovery Needs
Don't know what APIs you have? Salt Security, Akamai API Security, and Levo.ai can discover them from live traffic. If you already maintain OpenAPI specs, 42Crunch is a better fit.
Integration with Existing Tools
Already using Burp Suite for web testing? It handles API testing reasonably well. A dedicated API tool on top makes sense mainly if you need deeper coverage or runtime monitoring.
Compliance Requirements
For PCI DSS or HIPAA audits, you'll want tools that spit out compliance-ready reports without manual formatting. Akamai API Security and Cequence handle this well out of the box.
Frequently Asked Questions
What is API security?
What is the OWASP API Security Top 10?
How is API security different from DAST?
Do I need a separate API security tool?
What is API discovery?
Related API Security Resources
Explore Other Categories
API Security covers one aspect of application security tools. Browse other categories below.

Written & maintained by
Suphi CankurtEight years on the vendor side of application-security sales — thousands of evaluations and demos. I started AppSec Santa in 2022 to put that insider view to work for buyers. Independent of any vendor, paid by none, and honest about what fits whom.