Akto is an AI security platform for securing AI agents and MCP (Model Context Protocol) servers. Fortune 500 security teams and over 1,000 AppSec teams use it.
Ankita Gupta (CEO) and Ankush Jain (CTO) founded the company in 2022. It started as an open-source API security tool, then pivoted to AI agent security in 2025.
Akto shipped one of the first dedicated MCP security solutions in June 2025 and launched the full Agentic Security Platform in September 2025.
What is Akto?
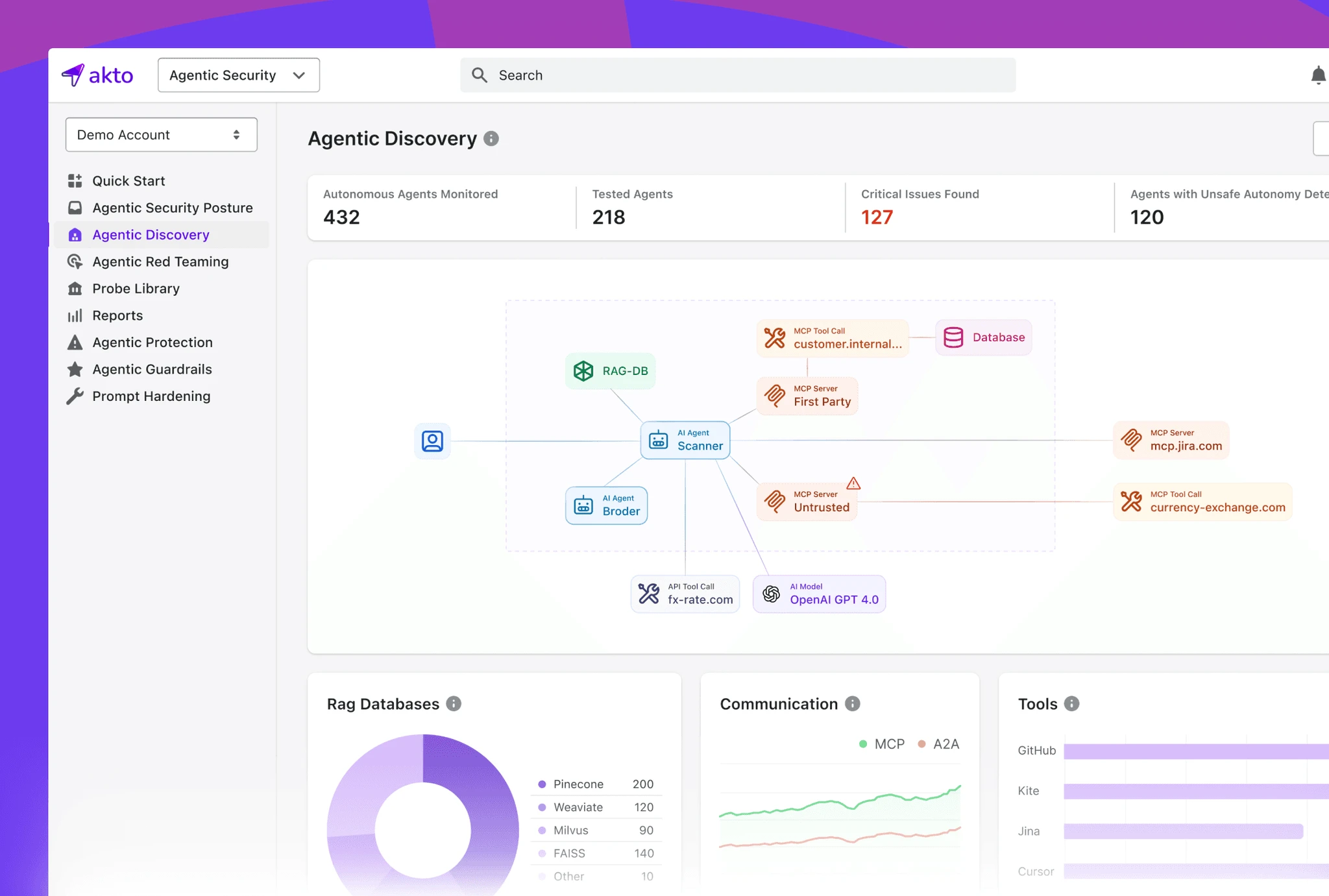
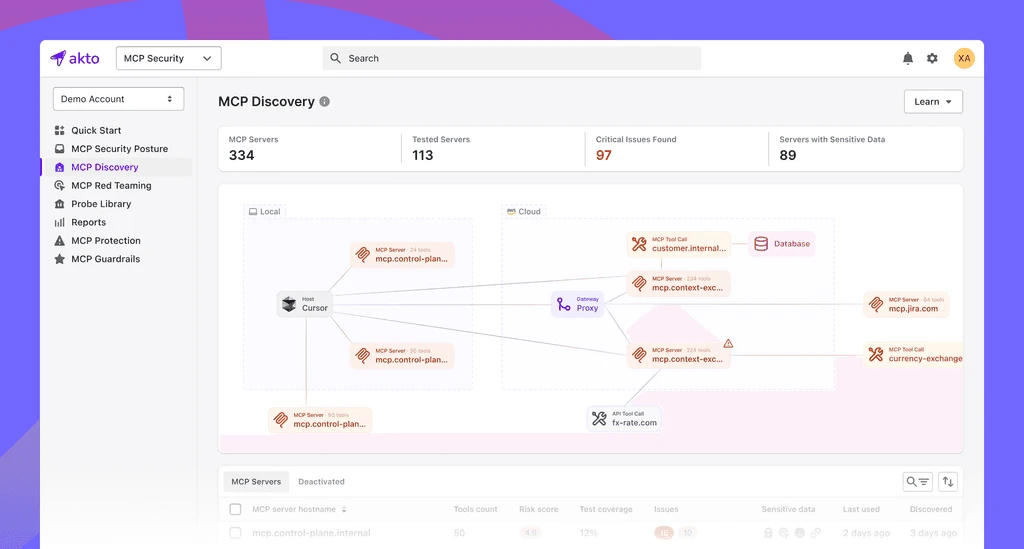
Akto’s platform does three things: discovers your AI agents and MCP servers, red teams them, and enforces runtime guardrails.
It inventories every AI agent and MCP tool in your infrastructure, runs attack simulations against them, and blocks risky agent behavior at runtime. The 50+ traffic and code connectors cover both cloud and on-prem environments.
What are Akto’s key features?
| Feature | Details |
|---|---|
| AI Agent Discovery | MCP servers, agents, tools, resources with lineage tracking |
| Attack Library | 1,000+ real-world agent exploits (AI Agent Attack Matrix) |
| Red Teaming | Automated via Agent Probe |
| Threat Detection | Prompt injection, tool poisoning, poisoned memory, cascading hallucinations |
| Runtime Protection | Guardrails, behavior drift detection, access anomaly detection |
| Connectors | 50+ traffic and code connectors |
| MCP Tools | MCP Endpoint Shield, MCP Recon |
| API Security | Legacy open-source platform (MIT license, 1.4k GitHub stars) |
Agentic visibility and discovery
Akto finds every MCP server and AI agent your developers deploy. The connectors build an inventory of agents, MCP servers, tools, and data sources across cloud providers and on-prem environments.
Lineage tracking maps dependencies between agents — which tools each agent can access, which data sources it touches. That matters because a single compromised MCP server could give an attacker access to multiple downstream agents.
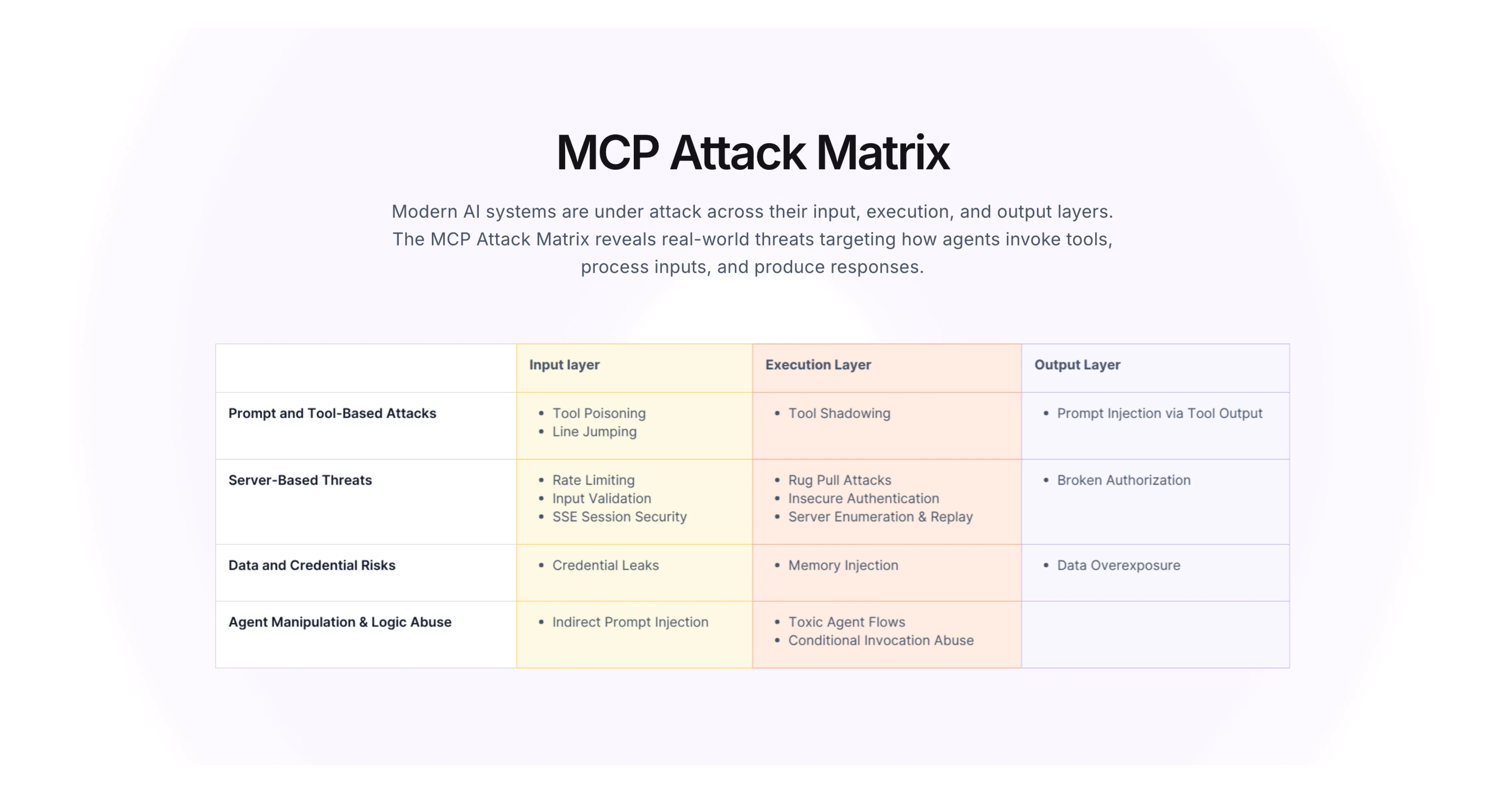
AI Agent Attack Matrix
The red teaming engine uses the AI Agent Attack Matrix, a library of 1,000+ real-world agent exploits covering:
- Prompt injection — testing whether agents follow malicious instructions embedded in data
- Tool poisoning — checking if agents can be tricked into misusing tools
- Poisoned memory — exploiting agent memory to influence future behavior
- Cascading hallucinations — triggering chain reactions across multi-agent systems
- Unauthorized tool use — agents accessing tools outside their intended scope
- Risky multi-step chains — complex agent workflows where failures compound
Agent Probe runs these attacks continuously, not as a one-time scan.
Runtime guardrails
The guardrails enforce enterprise policies at runtime. If an agent attempts something risky, the guardrails block it before execution.
The system also watches for behavior drift and flags unusual access patterns.
Legacy API security
The original API security tool is still available as open-source under MIT license. It offers:
- Automatic API discovery via traffic mirroring
- 1,000+ pre-built API security tests (OWASP API Top 10 , HackerOne Top 10)
- Custom test creation in YAML
- Docker Compose, AWS/GCP deployment
- Featured at Black Hat Arsenal 2023 and DEF CON 2023
The API security tool has 1.4k GitHub stars and 10K+ Docker pulls.
How do I get started with Akto?
When to use Akto
Akto targets organizations running AI agents and MCP servers in production, particularly enterprise teams where multiple agents interact with sensitive data and tools.
What are alternatives to Akto?
Akto sits at the intersection of AI agent security and MCP runtime protection. Closest alternatives split by which layer of the agent stack they own:
- Cisco DefenseClaw — Governance superset spanning policy, runtime enforcement, and audit across agentic AI. A fit when the requirement is enterprise-wide agentic AI governance rather than discovery + red-team-driven testing.
- Cerbos — Authorization-layer policy engine for AI agents, complementing rather than replacing discovery and exploit testing. A fit when fine-grained agent authorization is the gap.
- Agentic Radar — Open-source workflow scanner for LangGraph, CrewAI, OpenAI Agents, AutoGen, and n8n. A fit when developer-time scanning of agentic workflow code matters more than runtime guardrails.
- Lakera Guard — Runtime API for prompt injection detection and content filtering on live agent traffic. A fit when prompt-injection blocking is the lead requirement and discovery is already handled elsewhere.
For the wider AI security landscape, see the AI security tools guide. For open-source LLM security testing without the enterprise platform, look at Garak or Promptfoo .
For prompt injection detection as an API, check Lakera Guard .