Akamai API Security is a platform-agnostic API security tools product that discovers APIs enterprise-wide, tests them in CI/CD pipelines, and detects runtime attacks using machine learning. It was previously sold as Noname Security , which Akamai acquired in June 2024 for $450 million.
The platform is vendor-neutral. It does not require Akamai’s CDN or any other Akamai product, though a native connector is available for Akamai Cloud customers.
It works across SaaS, hybrid, and on-premises environments with multiple CDNs, WAFs, and gateways.
Akamai was named a Leader across four categories (Overall, Product, Innovation, and Market) in the 2025 KuppingerCole Leadership Compass for API Security and Management. Published customer stories include Godrej, Novant Health, and Commerzbank (which secured 6 billion monthly API calls through the platform).
What is Akamai API Security?
The platform works in four stages: Discover, Test, Detect, and Respond.
API Security is a standalone product. When paired with Akamai App & API Protector, the two work together for inline blocking plus enterprise-wide visibility.
But App & API Protector focuses on traffic through Akamai Cloud, while API Security covers all API endpoints regardless of where they’re hosted.
What are Akamai API Security (Noname)’s key features?
| Feature | Details |
|---|---|
| API Discovery | Shadow, zombie, GenAI, LLM, and MCP server APIs. Continuous, not on-demand |
| CI/CD Testing | 200+ dynamic tests simulating malicious traffic against OWASP API Top 10 |
| Runtime Detection | ML-based behavioral anomaly detection across all API traffic |
| Traffic Coverage | Both east-west (internal) and north-south (external) API traffic |
| Posture Management | OWASP API Top 10 compliance with business logic visualization |
| Compliance | PCI DSS v4.0, GDPR, ISO 27001, HIPAA, FAPI, MITRE ATT&CK |
| Deployment | Platform-agnostic: SaaS, hybrid, on-prem. Multiple CDNs, WAFs, gateways |
| Sensitive Data | PII, IP, and internal documentation detection with obfuscated traffic samples |
| Managed Service | Optional Akamai security experts for continuous monitoring and response |
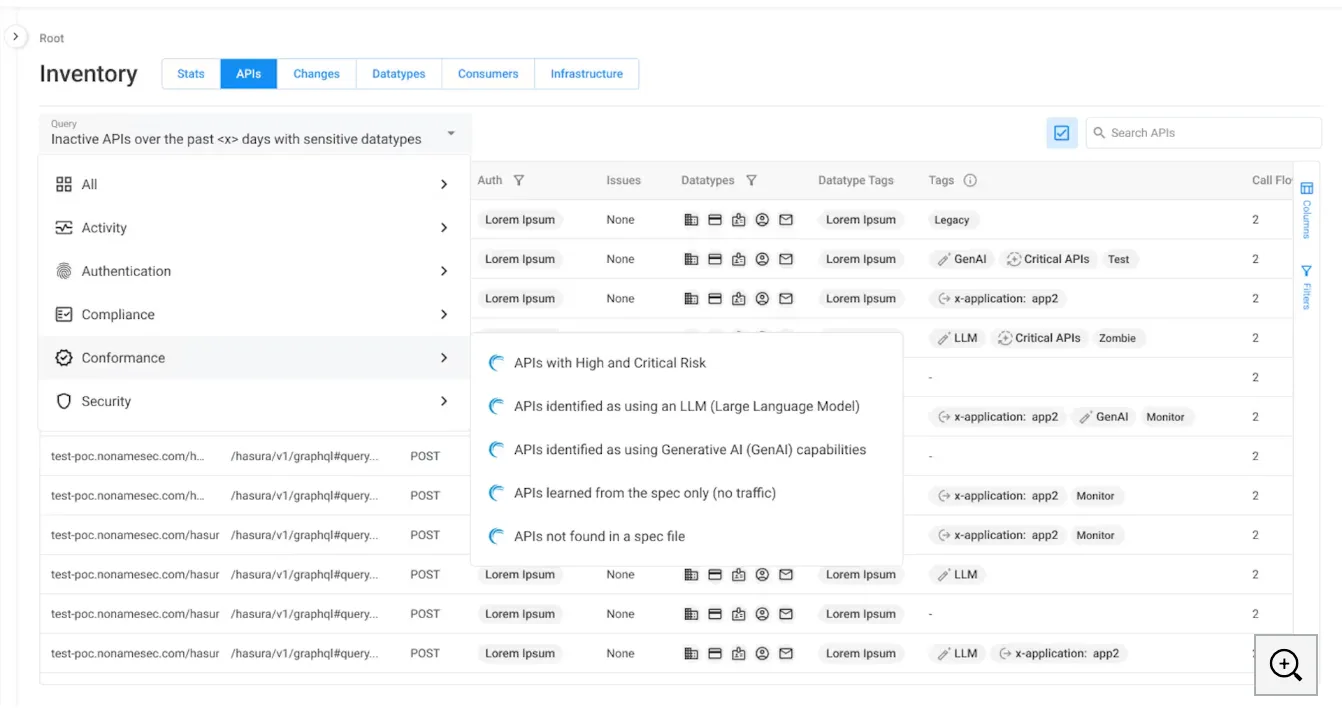
API Discovery
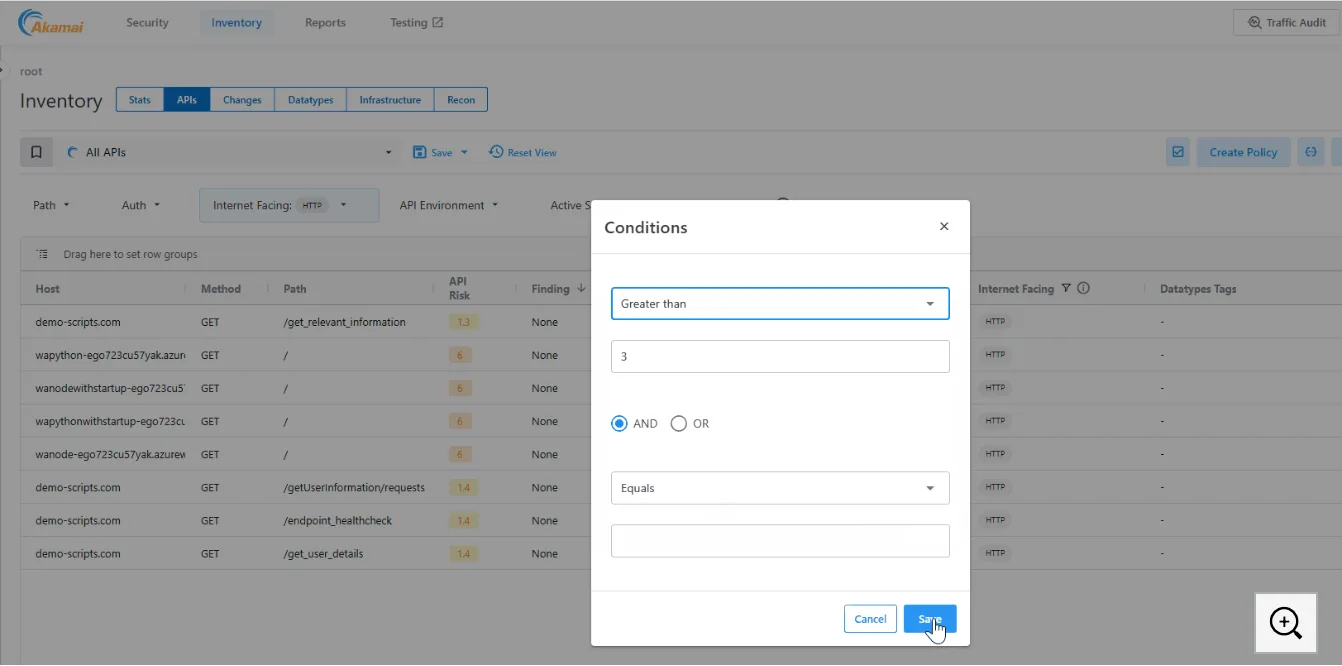
Discovery runs continuously, not on a daily or on-demand schedule. The platform finds new APIs and changes to existing ones around the clock.
What it identifies:
- All API endpoints across the enterprise, including shadow APIs deployed without security team knowledge
- APIs connecting to GenAI models, LLMs, and AI services, including unmanaged endpoints
Akamai API Security is platform-agnostic. It works across multiple CDNs, WAFs, and gateways in complex distributed environments.
A native Akamai CDN connector sends a copy of cloud traffic to API Security for analysis without adding latency, but the product does not require Akamai infrastructure.
Posture Management
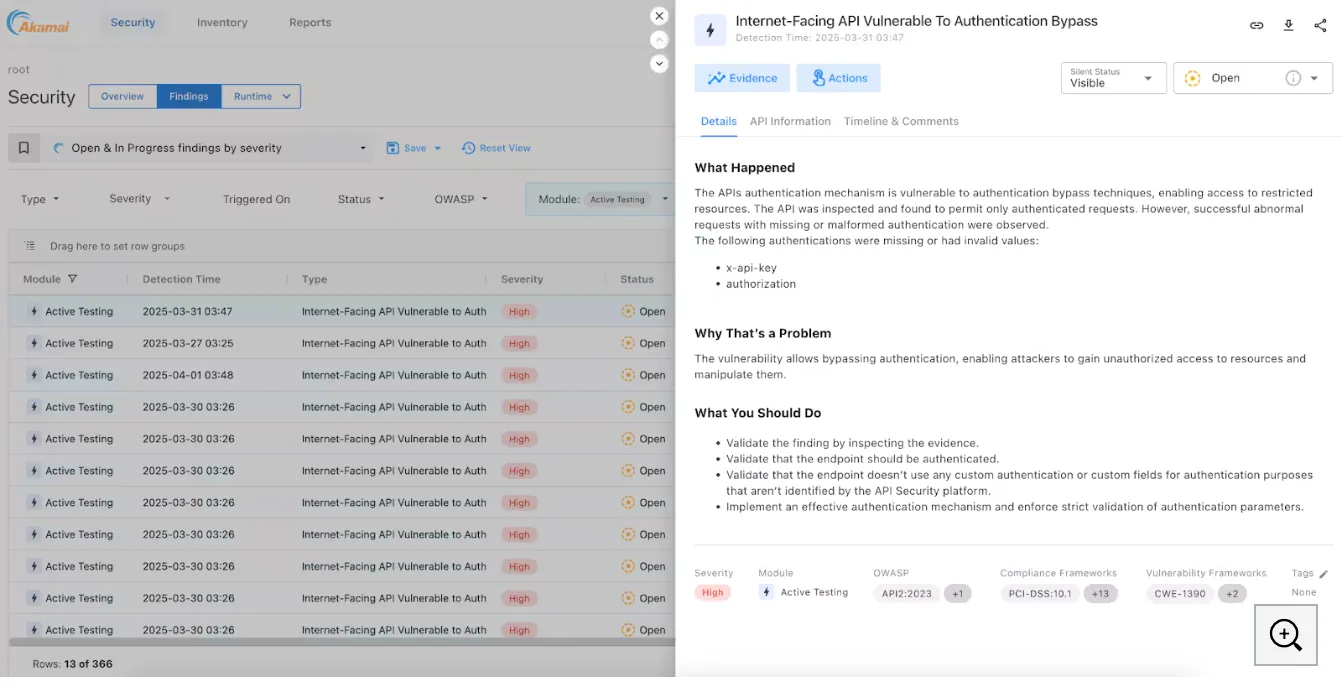
The posture engine analyzes APIs for OWASP API Top 10 vulnerabilities and misconfigurations. It generates two types of issues:
- Posture findings — verified misconfigurations and vulnerabilities found through analysis
- Runtime incidents — attacks that result from those misconfigurations
The system also automatically generates posture findings from confirmed runtime incidents, closing the loop between detection and prevention.
Visualizations map business logic, physical network infrastructure, and API traffic flows so security, development, and operations teams can see how APIs are used or misused.
Compliance Dashboard
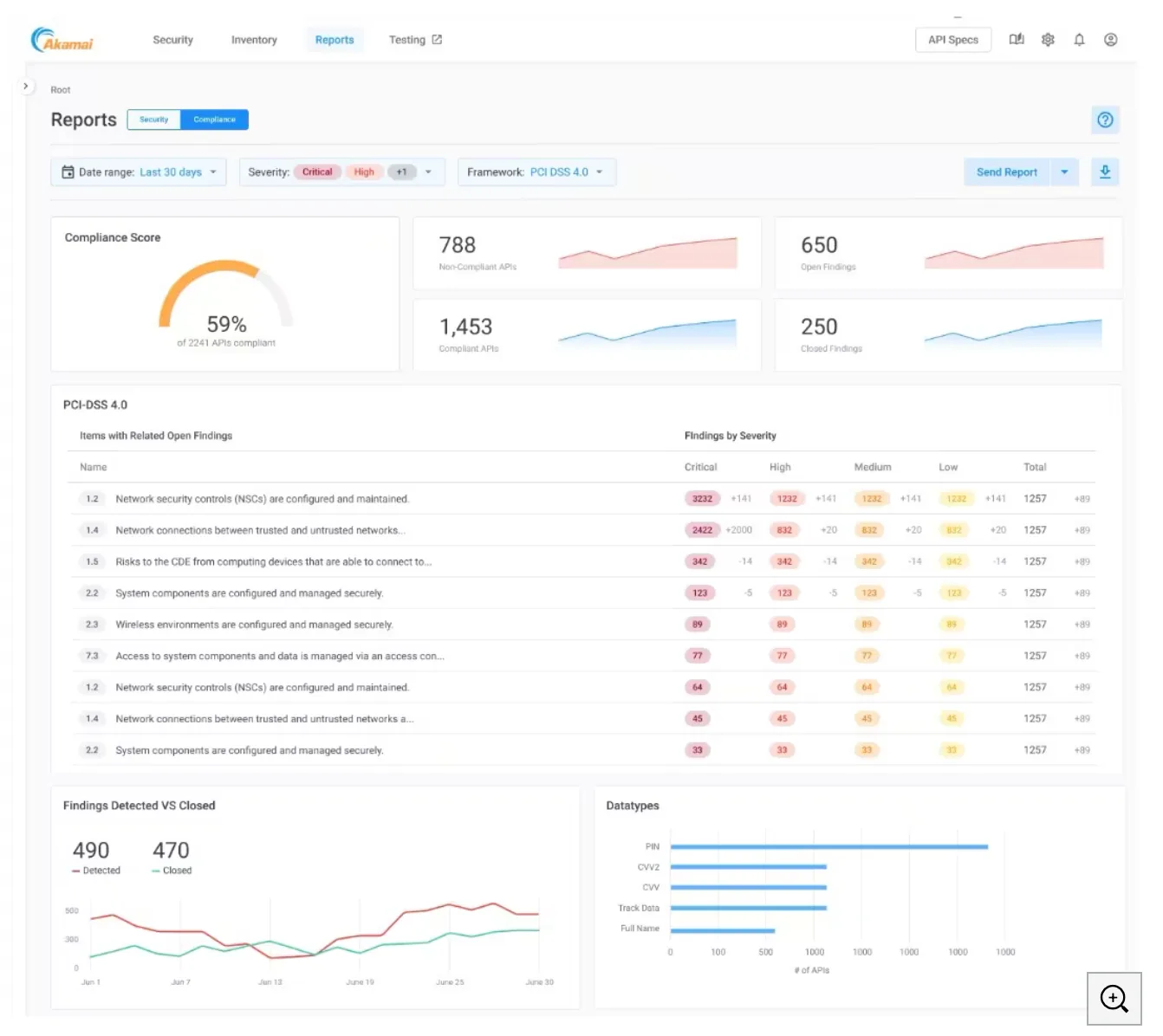
The Compliance Dashboard provides a centralized view of how your APIs align with security and privacy frameworks:
- PCI DSS v4.0
- GDPR
- ISO 27001
- HIPAA
- FAPI (Financial-grade API)
- MITRE ATT&CK vulnerability framework
CI/CD Testing
API testing integrates into existing CI/CD pipelines. The test engine runs 200+ dynamic tests that simulate malicious traffic, including all OWASP API Top 10 attack patterns.
Tests can be scheduled to run automatically at any stage of development.
This is a shift-left capability. The goal is catching vulnerabilities like business logic abuse before APIs reach production, not after.
Runtime Threat Detection
ML models baseline normal API behavior and flag deviations. Common attack types the platform detects:
- Business logic abuse — exploits in application design that cause unexpected behavior
- Unauthorized data access — broken authentication and authorization mechanisms
- Account takeover — credential theft and cross-site scripting attacks against APIs
- Data scraping — wholesale capture of large datasets through API queries
- Business denial of service — unrestricted API calls causing service degradation
Sensitive Data Management
API Security identifies which APIs contain PII, internal documentation, intellectual property, and other sensitive data. All traffic samples are obfuscated by default and only viewable by administrators and contributors.
What does Akamai API Security (Noname) integrate with?
Akamai CDN Native Connector
For Akamai Cloud customers, a native connector sends a copy of API traffic to API Security for analysis. The integration is built directly into both products, eliminating latency.
The connector automatically discovers and tracks APIs across Akamai-managed environments and can block attackers at the edge.
Deployment Options
API Security is platform-agnostic and deploys in any environment:
- SaaS — cloud-hosted analysis
- Hybrid — mix of cloud and on-premises components
- On-premises — fully self-hosted for data sovereignty requirements
It works with multiple CDNs, WAFs, and gateways simultaneously. Traffic mirroring sends a copy of API traffic for out-of-band analysis without affecting production performance.
Managed Security Service
Akamai offers a Managed Service for API Security that augments your SOC team with Akamai API security experts for continuous monitoring and rapid threat response. This includes 24/7 monitoring, alert investigation, and remediation workflows.
How do I get started with Akamai API Security (Noname)?
When to Use Akamai API Security
Akamai API Security fits organizations with large, distributed API estates that span multiple clouds, gateways, and CDN providers. It’s built for environments too complex for a single-vendor inline solution to cover.
Good fit if:
- You operate APIs across multiple clouds, CDNs, and gateways and need unified visibility
- You want to discover GenAI, LLM, and MCP server APIs alongside traditional REST endpoints
- You need compliance dashboards for PCI DSS v4.0, GDPR, HIPAA, or ISO 27001
- You want CI/CD testing with 200+ dynamic tests against OWASP API Top 10
- You already use Akamai CDN and want native integration without added latency
- You need both east-west and north-south API traffic monitoring
Consider alternatives if:
- You have a small number of APIs and need a simpler solution
- You want spec-driven API security starting from OpenAPI definitions — tools like 42Crunch focus on that
- You prefer open-source tools with fully self-managed infrastructure
- You need a standalone WAF with API bolt-on rather than a dedicated API security product
How to use Akamai API Security
The platform follows the four-stage Discover/Test/Detect/Respond model, and the most efficient onboarding I have seen mirrors that order.
First, connect data sources. Most teams start by mirroring API traffic from existing gateways, WAFs, or load balancers; Akamai Cloud customers can flip on the native CDN connector instead, which sends an out-of-band copy of edge traffic without latency overhead. The platform-agnostic deployment is what makes Akamai API Security usable in multi-CDN environments where neither Cloudflare API Shield nor Imperva API Security would cover the full estate.
Second, run discovery. The inventory builds continuously, surfacing shadow APIs, zombie APIs, and GenAI/LLM/MCP-tagged endpoints. The discovery output is the data foundation for everything else, so leave it running for at least a representative traffic window before tuning detection rules.
Third, review the posture findings against the OWASP API Top 10 and the compliance dashboard for PCI DSS v4.0, GDPR, ISO 27001, HIPAA, and FAPI. This is also where business-logic visualization helps cross-team conversations, because the map shows infrastructure, traffic, and API relationships in one view.
Fourth, configure runtime detection. The ML models baseline normal behavior, then flag broken authorization attempts, credential abuse, scraping, and business-logic exploits. Tune the rules against your existing SIEM/SOAR thresholds.
Fifth, integrate with CI/CD. The 200+ dynamic test suite targets OWASP API Top 10 patterns and runs at any pipeline stage, which closes the loop between runtime findings and shift-left coverage.
Akamai API Security pricing
Akamai does not publish pricing for API Security. The product follows the standard Akamai enterprise commercial model — contact sales for a quote, with cost driven by API call volume, the number of monitored environments, and which add-ons (Managed Security Service, App & API Protector pairing, advanced compliance modules) are included.
For existing Noname Security customers, Akamai has continued the platform under the new brand. Renewal terms and migration pricing are negotiated through Akamai’s sales organization rather than published rate cards.
Three signals usually move the price: API call volume across the monitored environment, the number of CDNs/WAFs/gateways the platform spans, and whether you bundle the Managed Security Service for 24/7 SOC augmentation. Teams already invested in Akamai’s edge often see better packaging than greenfield buyers because adjacent products (Bot Manager, App & API Protector, Kona Site Defender) can roll into a multi-product agreement.
Akamai API Security alternatives
Akamai API Security is a platform-agnostic, runtime-first product. The closest alternatives swap one of those two axes.
Salt Security sits in the same runtime, behavior-based niche but does not lean on edge ownership. If you want behavioral API security without an Akamai relationship — or you have evaluated Akamai and prefer a pure-play API Security vendor — Salt is the canonical comparison.
42Crunch takes the opposite architectural stance: contract-first, design-time-leaning, audit-driven. Teams that already maintain OpenAPI specs and want to enforce them at runtime through the micro API firewall pick 42Crunch instead of (or alongside) Akamai.
Wallarm bundles WAAP heritage with API discovery and runtime detection. It is a solid fit when the WAF replacement decision and the API security decision are the same purchase.
Imperva API Security follows the same WAF-platform extension pattern. Existing Imperva WAF customers will usually evaluate this before going to Akamai.
Cequence leads with a unified API protection platform tailored to bot abuse and business-logic attacks — closer to Akamai in scope, with a stronger posture toward L7 abuse than CDN-edge protection.
If you already operate behind Cloudflare’s edge, Cloudflare API Shield bundles API security into the CDN tier and may bypass the multi-CDN advantage that drives the Akamai purchase. The buying signal that favors Akamai over each of these is platform-agnostic deployment across more than one cloud, gateway, or CDN.