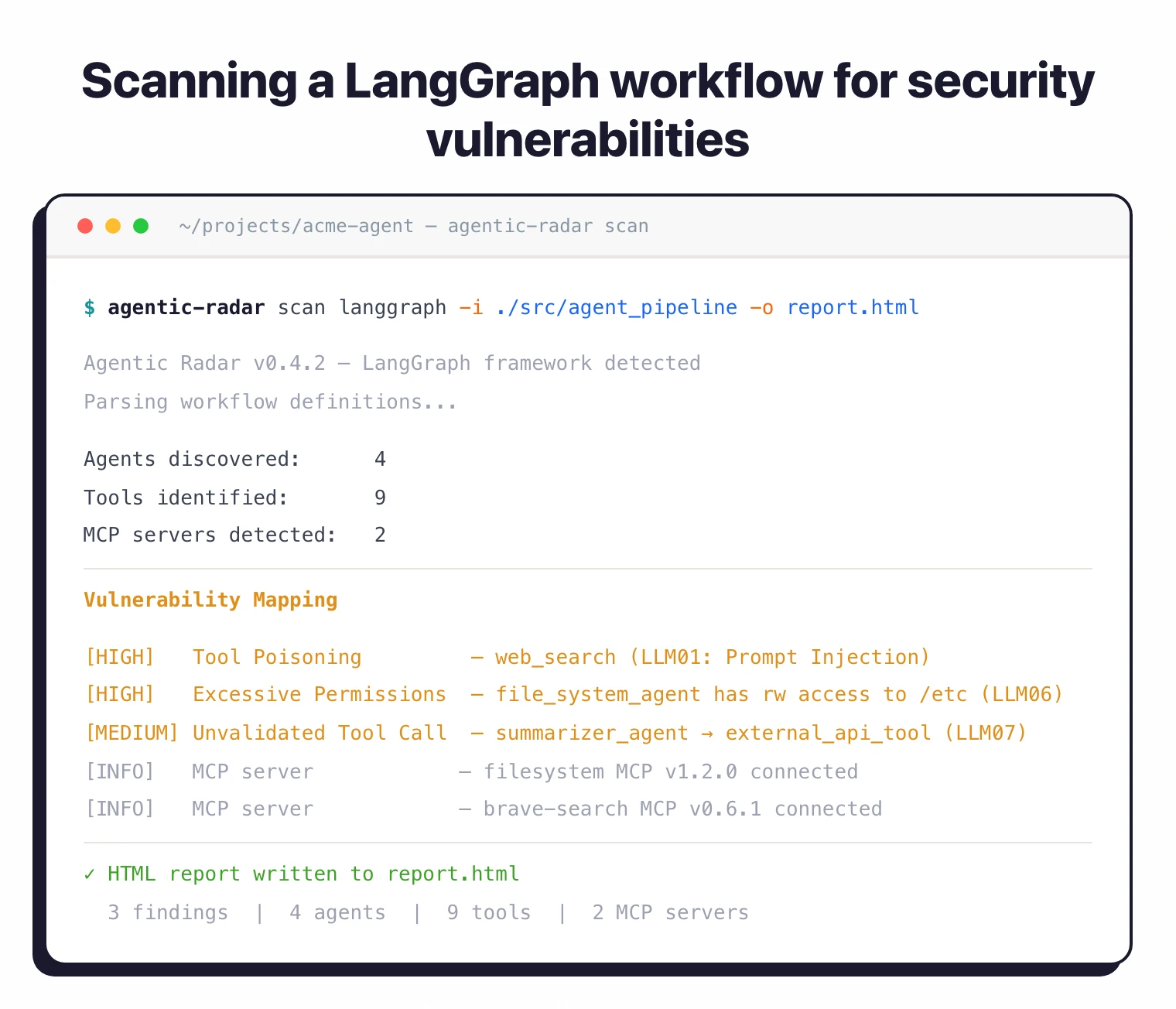
Agentic Radar is an open-source CLI security scanner that analyzes LLM-based agentic workflows for vulnerabilities across five major frameworks: LangGraph, CrewAI, OpenAI Agents SDK, AutoGen, and n8n.
Unlike component-level scanners such as MCP-Scan , Agentic Radar takes a system-level view — parsing entire workflow definitions, generating visual dependency graphs, and mapping risks to OWASP security frameworks.
Built by SPLX AI — a company focused on end-to-end AI security — Agentic Radar was released in March 2025 as one of the first tools purpose-built for scanning agentic AI architectures.
While individual components like MCP servers have their own scanners, Agentic Radar takes a broader view: analyzing the entire workflow to understand how agents connect, what tools they access, and where security gaps exist in the system as a whole.
The tool supports five major agentic frameworks: LangGraph, CrewAI, OpenAI Agents SDK, AutoGen, and n8n.
What is Agentic Radar?
Agentic AI systems are inherently complex — multiple agents coordinate across tools, APIs, and data sources, often with chained decisions where one agent’s output becomes another’s input. Traditional security tools that analyze individual components miss the systemic risks that emerge from these interactions.
Agentic Radar addresses this by parsing the full workflow definition, mapping every agent-to-tool and agent-to-agent connection into a dependency graph, and then analyzing that graph for vulnerabilities. The output is an HTML report that security teams can share and review without needing to understand the underlying framework code.
What are Agentic Radar’s key features?
| Feature | Details |
|---|---|
| Supported Frameworks | LangGraph, CrewAI, OpenAI Agents SDK, AutoGen, n8n |
| Dependency Graphs | Visual agent-tool-MCP connection mapping |
| OWASP Mapping | LLM Top 10 + Agentic AI Threats and Mitigations |
| MCP Server Detection | Identifies all MCP servers used by agents |
| Tool Identification | Lists external and custom tools per agent |
| Prompt Hardening | LLM-assisted system prompt security refinement (OpenAI Agents, CrewAI, AutoGen) |
| Runtime Testing | Simulated adversarial inputs — prompt injection, PII leakage, harmful content (OpenAI Agents only) |
| Custom Tests | YAML-based test definitions with custom inputs and success conditions |
| Report Format | Shareable HTML reports (sample report ) |
| CI/CD | GitHub Actions workflow for automated scanning on code changes |
| Installation | pip install agentic-radar with optional framework extras |
| Requirements | Python 3.10-3.12 for CrewAI extras |
| License | Apache 2.0 |
Framework feature matrix
Feature coverage varies by framework:
| Framework | Scan | MCP Detection | Prompt Hardening | Runtime Testing |
|---|---|---|---|---|
| OpenAI Agents | Yes | Yes | Yes | Yes |
| CrewAI | Yes | Yes | Yes | No |
| AutoGen | Yes | Yes | Yes | No |
| LangGraph | Yes | Yes | No | No |
| n8n | Yes | Yes | No | No |
Dependency graph analysis
The core of Agentic Radar is its ability to parse framework-specific code (LangGraph state graphs, CrewAI crew definitions, n8n workflow JSON, etc.) and produce a unified dependency graph. This graph shows which agents can communicate with each other, what tools each agent has access to, which MCP servers are connected, and how data flows through the system.
For security teams, this graph answers critical questions: Can a compromised tool in Agent A affect Agent B? Does any single agent have excessive tool access? Are there unsanctioned MCP servers connected to the workflow?
Prompt hardening
Beyond scanning for existing vulnerabilities, Agentic Radar can proactively improve your agent security. The prompt hardening feature analyzes system prompts across your workflow and uses LLM assistance to refine them — adding input validation instructions, tightening scope boundaries, and removing patterns that make prompts susceptible to injection attacks. Currently supported for OpenAI Agents, CrewAI, and AutoGen frameworks.
Runtime testing
For deeper security validation, Agentic Radar can execute simulated adversarial inputs against your agents to test their resilience. This includes prompt injection attempts, PII leakage probes, harmful content generation, and misinformation injection. Tests can be customized via YAML configuration files with specific inputs and expected outcomes.
SBOM analysis
Beyond workflow-level scanning, Agentic Radar includes software bill of materials (SBOM) analysis that identifies known CVEs in the dependencies used by your agentic system. This connects traditional supply chain security with AI-specific vulnerability detection, giving teams a unified view of both infrastructure and agentic risks in a single report.
How do I get started with Agentic Radar?
pip install agentic-radar for the base package. Add framework-specific extras as needed: pip install "agentic-radar[crewai]" or pip install "agentic-radar[openai-agents]".When to use Agentic Radar
Best for development and security teams building multi-agent AI systems. Agentic Radar fills the gap between individual component scanners and manual security reviews of agent code.
If you are building multi-agent systems on any of the supported frameworks, running Agentic Radar during development and CI/CD gives you visibility into how the system connects and where risks hide.
The tool adds the most value during the design and review phase of agentic architectures — before deployment, when the dependency graph can reveal excessive permissions, unsanctioned tool access, or missing guardrails that are harder to fix once the system is in production.
For teams adopting multiple frameworks or migrating between them, the multi-framework support means a single tool covers the entire portfolio. The HTML report format also makes it easy to share findings with non-technical stakeholders who need to understand AI system risks without reading code.
What are alternatives to Agentic Radar?
Agentic Radar’s wedge is workflow-level scanning across multiple agentic frameworks. Tools that overlap on neighboring concerns:
- MCP-Scan — Component-scope scanner focused specifically on Model Context Protocol servers. A fit when MCP is the only attack surface you care about and you do not need framework-wide workflow analysis.
- invariant-labs/mcp-scan — Python alternative for MCP server scanning aligned with the Invariant security policies. A fit when you want a research-leaning Python library instead of a CLI tool.
- Cisco DefenseClaw — Enterprise governance superset that adds runtime policy enforcement, audit, and centralized control beyond static scanning. A fit when the requirement is full agentic-AI governance rather than developer-time scanning.
- Lakera Guard — Runtime API for prompt injection detection and content filtering on live agent traffic. A fit when you need to block attacks in production as a complement to Agentic Radar’s pre-deployment scan.
- Prompt Security — Runtime LLM firewall covering prompt injection, data leakage, and jailbreak detection across multiple LLM providers. A fit when the priority is runtime traffic inspection across heterogeneous model deployments.
For the wider AI security landscape, see the AI security tools guide.