7AI is an AI security platform that deploys autonomous AI agents to handle security operations center (SOC) work — alert triage, investigation, threat hunting, and incident response. Unlike traditional SOAR tools that execute pre-written playbooks, 7AI uses Dynamic Reasoning to investigate novel threats in real time without predefined rules.
Founded in 2024 by Lior Div and Yonatan Striem-Amit — the same team behind Cybereason — 7AI launched from stealth in February 2025 and raised a $130 million Series A by December 2025 (the largest cybersecurity Series A in history), bringing total funding to $166 million.
The company is headquartered in Boston, Massachusetts, with backing from Index Ventures, Greylock, CRV, Spark, and Blackstone Innovations Investments.
What is 7AI?
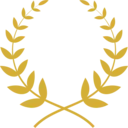
7AI is an agentic SOC platform: it deploys 60+ specialized AI agents that autonomously investigate security alerts end-to-end, from initial triage through cross-system correlation to a final determination — without waiting for a human analyst at each step.
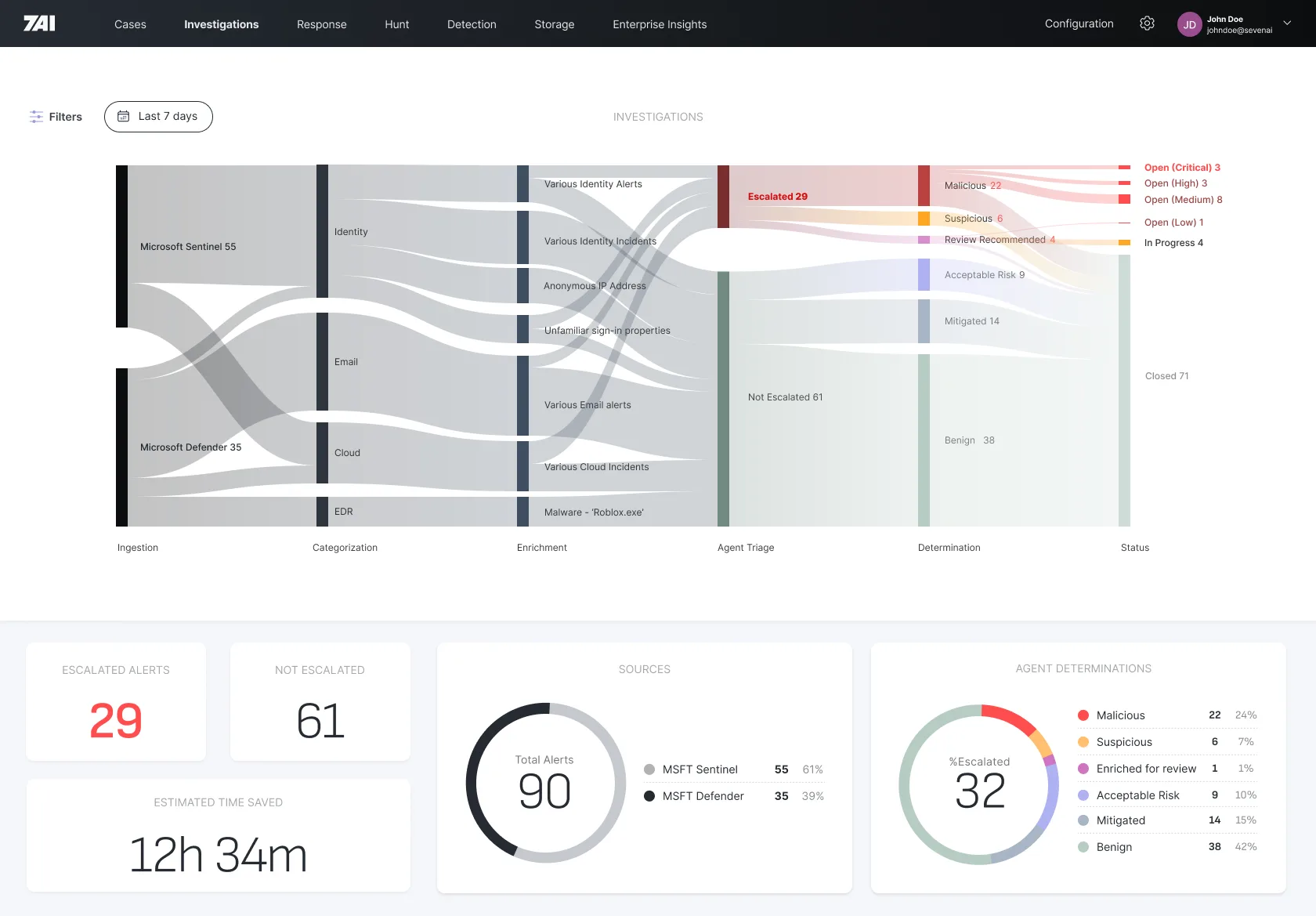
Instead of routing alerts through static playbooks, 7AI agents assess each alert’s context and determine their investigative strategy in real time, which is what allows them to handle novel threats that no playbook was written for.
In practice, 7AI replaces the manual, repetitive work that consumes most SOC analyst time. Rather than having human analysts triage thousands of alerts, enrich data across multiple tools, and correlate signals by hand, specialized agents swarm on each alert and work through the investigation autonomously.
60+ purpose-built agents cover five domains: Endpoint, Identity, Cloud, Email, and Network. Each handles specific investigative tasks — device enrichment, file provenance, user behavior, network traffic correlation.
As of early 2026, 7AI reports processing 5M+ alerts across its customer base, saving 732,910+ analyst hours (roughly 366 full-time analyst-years) and reclaiming $42.1M in SOC productivity value since launching in February 2025.
What are 7AI’s key features?
| Feature | Details |
|---|---|
| Agent Types | 60+ specialized agents across Endpoint, Identity, Cloud, Email, Network |
| Dynamic Reasoning | Real-time investigative strategy for novel and known threats |
| False Positive Reduction | 95-99% elimination in production deployments |
| Alert Processing | 5M+ alerts processed; 732,910+ analyst hours saved |
| Investigation Speed | Minutes instead of hours per investigation |
| SOC Productivity | $42.1M reclaimed value across customer base |
| Response Actions | Endpoint isolation, account disabling, IP blocking with human-in-the-loop |
| Integrations | 50+ tools (CrowdStrike, Splunk, Okta, AWS, Microsoft 365, etc.) |
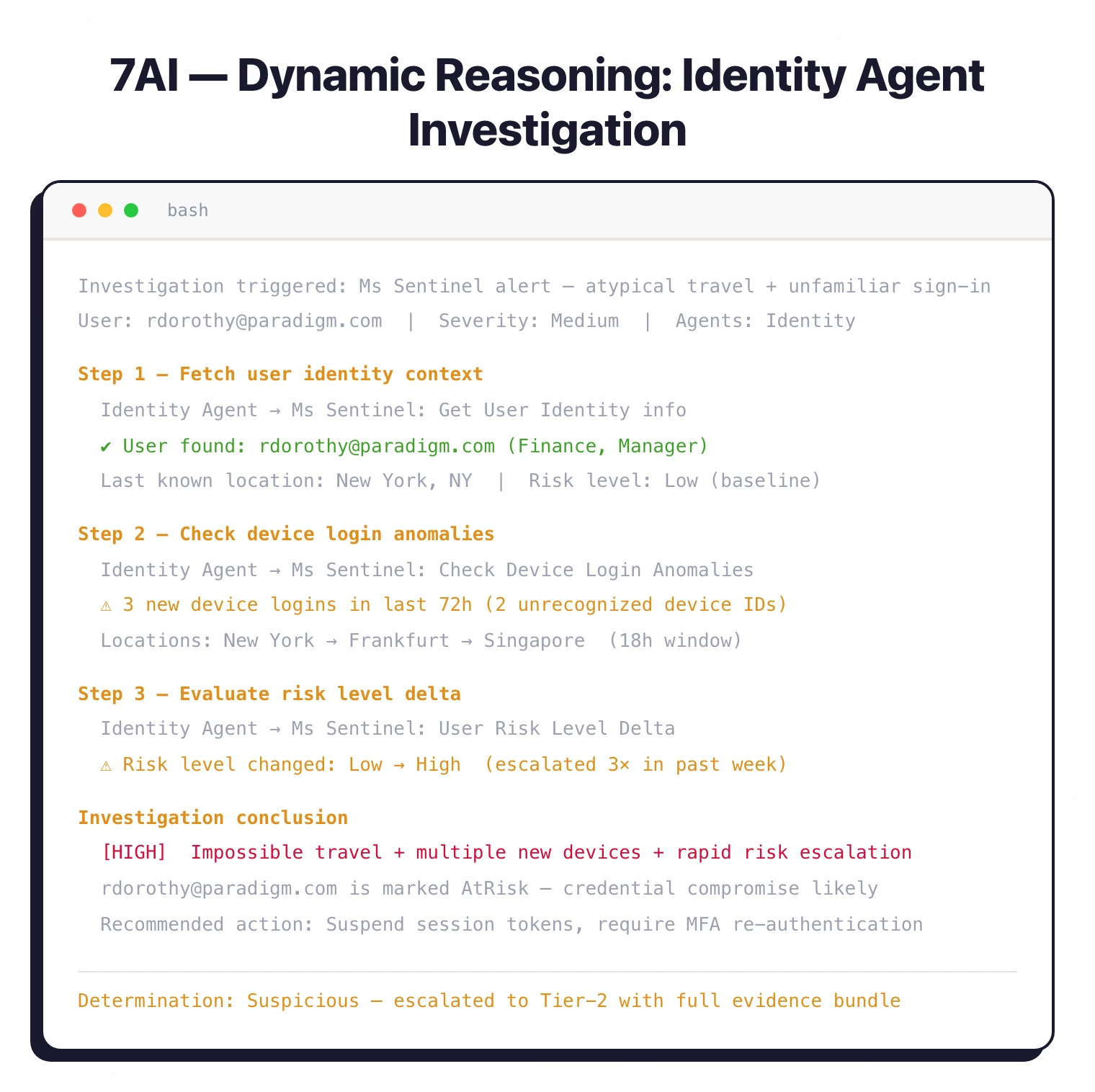
| Platform Modules | Cases, Investigations, Detection, Response, Hunting, Enterprise Insights |
| Threat Hunting | Proactive cross-system correlation with IOC extraction |
| Reporting | Real-time dashboards and board-ready security metrics |
| Deployment | Cloud-based platform with API integrations |
Dynamic Reasoning
Dynamic Reasoning is 7AI’s approach to investigating threats that don’t match any existing rule or signature. Traditional security automation follows a fixed path: if alert matches pattern X, execute playbook Y. That works for known threats but fails completely against novel attack techniques and zero-days. Dynamic Reasoning agents assess each alert’s context and determine their investigative strategy on the fly — which data sources to query, what correlations to check, how deep to go — based on what they find along the way.
Threats that don’t match any existing signature or rule get investigated just as thoroughly as known threats, turning attacker tactics into defensive intelligence rather than missed alerts.
Swarming agent architecture
Unlike SOAR tools that route an alert through a single sequential pipeline, 7AI deploys multiple specialized agents simultaneously on the same alert. An endpoint agent enriches device context, an identity agent checks user behavior, a network agent analyzes traffic — all in parallel. That swarming produces richer conclusions and faster results: investigations that would take a human analyst hours complete in minutes.
Enterprise Insights
Context-aware agents factor in organizational policies, user roles, and approved software when making decisions. An alert about unusual software installation gets checked against the company’s approved list before escalating — an approach that cuts false positives beyond what generic detection rules can achieve.
Enterprise Insights dashboards show alert volumes, agent performance, investigation outcomes, and posture trends in real time. Reports translate operational metrics into business impact language for board-level reporting.
How do I get started with 7AI?
When to use 7AI
Ideal for security teams drowning in alert volume — organizations where analysts spend most of their time on repetitive triage rather than strategic security work. It makes the biggest difference in large, distributed environments generating thousands of daily alerts across multiple security tools.
DXC Technology, one of 7AI’s early customers, deployed what they describe as the world’s largest agentic security operation in eight weeks, reporting an 80% reduction in tier-1 analyst time and a 95% drop in tickets requiring human analysis. BigID reported achieving 10x scaling of their security team capacity without adding headcount.
Deployment connects via API to your existing tools — no rip-and-replace required. Customers report going live in weeks, not months.
How 7AI compares to SOAR tools
Traditional SOAR platforms — Splunk SOAR, Palo Alto XSOAR, IBM Resilient — execute pre-written playbooks. An alert matches a pattern, the platform runs the matching response, and anything outside the rule library falls back to a human analyst.
7AI’s Dynamic Reasoning replaces the playbook step with agent-driven investigation. Rather than scripting every branch in advance, the platform’s agents pick which data sources to query, which correlations to test, and how deep to go based on what they find inside the alert.
The practical contrast lines up across three dimensions:
- Coverage of unknown threats — SOAR handles known patterns; 7AI’s agents reason through novel signals without a pre-existing rule.
- Maintenance overhead — SOAR playbooks need ongoing curation as the threat surface shifts; Dynamic Reasoning adapts without rule rewrites.
- Decision visibility — SOAR shows which rule matched; 7AI shows the chain of investigative steps the agents took, including dead ends.
Teams already running SOAR rarely rip it out — most pair it with 7AI so the playbooks keep handling routine triage while agents take the ambiguous cases.
What are alternatives to 7AI?
7AI sits in the agentic SOC and SOAR-replacement space. The closest alternatives split along whether they replace the playbook layer with agents or extend it with AI assistance:
- Torq — Hyperautomation platform with AI-augmented playbooks. A fit when you want pre-built integrations and visual workflow editing rather than autonomous investigation.
- Tines — No-code automation for security operations. A fit when ease of authoring deterministic workflows matters more than open-ended reasoning.
- Prophet AI Security — AI-driven alert triage built around a closed-loop reasoning engine. A fit when the priority is tier-1 triage compression on a single alert stream.
- Dropzone AI — Autonomous SOC analyst that investigates alerts end-to-end. A fit when the deployment scope is narrower (single SIEM ingest) and the team wants a packaged analyst replacement.
For the wider AI security landscape, see the AI security tools guide. For AI-focused threat detection in code and models rather than SOC operations, consider Protect AI Guardian or CalypsoAI .