42Crunch is an API security tools platform that audits OpenAPI specifications, tests live APIs for conformance, and deploys micro firewalls for runtime protection. Its IDE extensions have been used by over 1.6 million developers across VS Code, JetBrains, and Eclipse.
The company was founded in 2016 by Jacques Declas and Isabelle Mauny. It is headquartered in London and backed by a $17M Series A round led by Energy Impact Partners, with Adara Ventures participating.
What is 42Crunch?
42Crunch covers the API security lifecycle from design through runtime. The platform works in three stages: audit your OpenAPI spec before deployment, scan the running API for conformance issues, and then protect it with a micro firewall that enforces the contract in production.
Unlike traffic-based API security tools that analyze behavior after deployment, 42Crunch starts with the OpenAPI definition itself. The spec becomes the single source of truth for what the API should accept, return, and block.
What are 42Crunch’s key features?
42Crunch’s 300+ checks include OWASP API1:2023 broken object-level authorization (BOLA) test cases — the vulnerability class that has dominated real-world API breaches since the OWASP API Top 10 first added it in 2019. Schema-injection, parameter-injection, and authorization-test families all map back to BOLA / broken authorization testing patterns rather than generic input fuzzing.
The platform handles shadow API discovery by scanning runtime traffic against the registered OpenAPI contract — endpoints that respond to traffic but do not appear in the spec are flagged as undocumented or shadow APIs. Because the model is contract-first, “shadow” here means anything not declared in OAS, which is a tighter definition than the network-traffic discovery used by Salt Security or Akamai API Security.
| Feature | Details |
|---|---|
| Security Audit | 300+ checks on OpenAPI v2, v3.0, v3.1 definitions |
| Audit Scoring | 0-100 score (30 pts security, 70 pts data validation) |
| Conformance Scan | Dynamic testing with happy path, unhappy path, and custom tests |
| Micro API Firewall | Positive security model based on OpenAPI contract enforcement |
| IDE Support | VS Code, 19+ JetBrains IDEs, Eclipse |
| CI/CD Integration | GitHub Actions, GitLab, Azure Pipelines, Jenkins, Bitbucket, Bamboo, Tekton |
| API Contract Generator | Converts Postman Collections and HAR files to OpenAPI specs |
| File Support | JSON and YAML, up to 10 MB per file |
API Security Audit
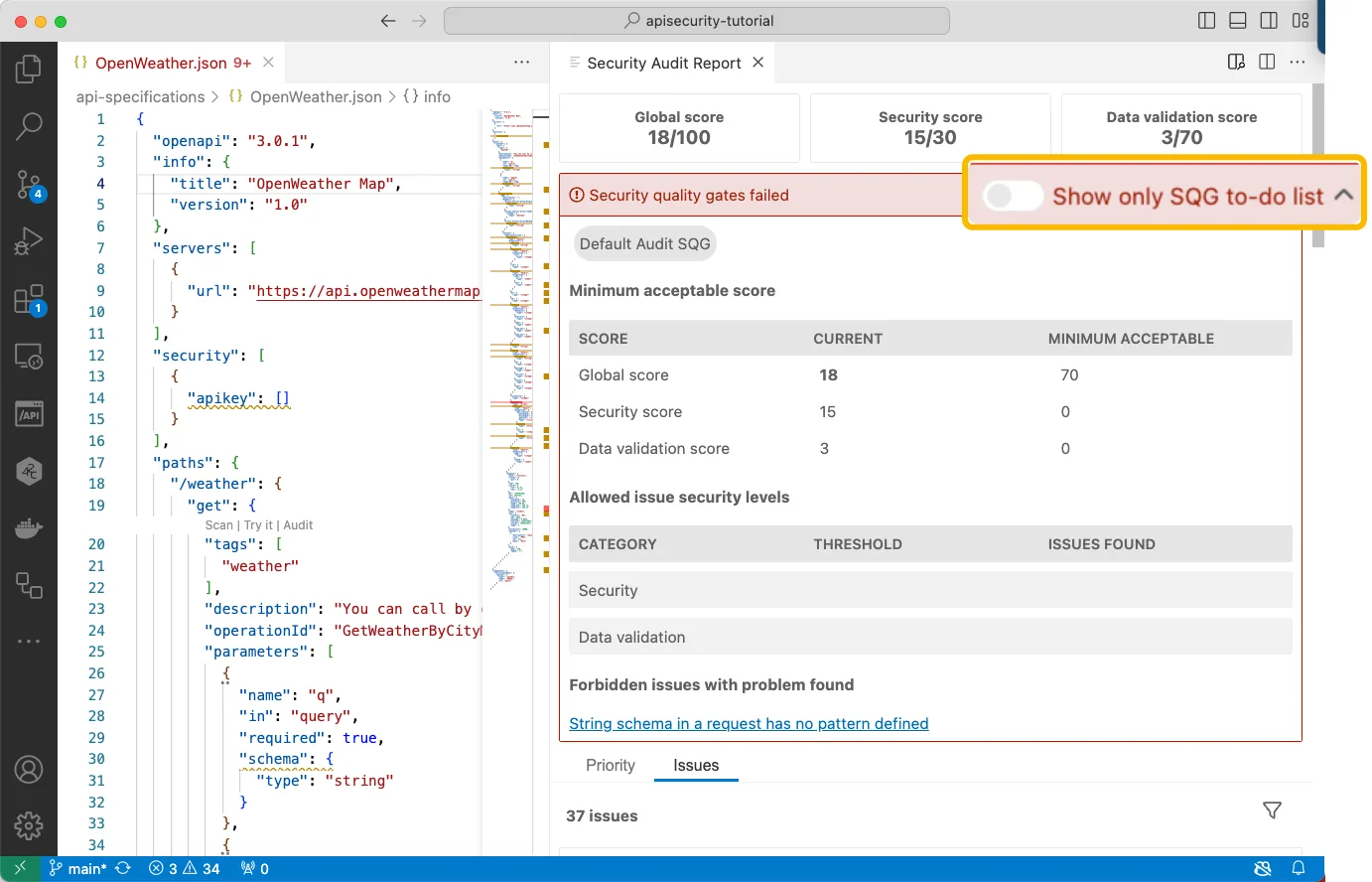
Security Audit performs static analysis on OpenAPI definitions. It runs over 300 checks across three categories:
- Security definitions — evaluates authentication methods, authorization schemes, and transport security (up to 30 points)
- Data validation — assesses input/output schemas, data constraints, and format enforcement (up to 70 points)
- OpenAPI format — checks structural validity and adherence to OpenAPI specification rules
The audit follows up to six consecutive JSON schema references when calculating scores. Each issue found deducts points based on severity, and sensitivity multipliers adjust deductions based on operation risk levels.
42Crunch recommends a minimum audit score of 70 before running conformance scans. APIs scoring below that threshold lack sufficient security definitions for reliable firewall protection.
API Conformance Scan
Conformance Scan generates real traffic against live API endpoints. It follows a four-stage process:
- Preparation — parses the OpenAPI definition, generates parameter values, verifies authentication, and checks endpoint availability
- Happy path tests — sends valid requests to confirm baseline behavior (expects HTTP 200-399 or 404)
- Test generation — creates test payloads based on happy path responses
- Scan execution — sends test requests at a constant rate and analyzes responses
The scan engine supports multiple test types:
- Happy path tests — baseline validation with valid inputs
- Conformance tests — schema injection, parameter injection, header injection, and HTTP method tests
- Unhappy path tests (v2 engine) — error scenario testing with expected 4XX responses
- Custom tests (v2 engine) — user-defined tests for specific implementation scenarios
- Drift scan (v2 engine) — lightweight monitoring to verify deployed APIs maintain expected behavior
Parameter values are generated automatically from OpenAPI constraints. Standard formats like dates, emails, IPs, and UUIDs follow RFC specifications.
Developers can override defaults using x-42c-sample, default, enum, or example properties.
42Crunch states that invasive scans should only run against APIs you own, and only against non-production systems. Drift scans are the exception — those are approved for production.
Micro API Firewall
API Protection deploys a micro firewall in front of each API. It enforces the OpenAPI contract on every incoming and outgoing transaction using a positive security model.
The firewall creates an allowlist from the API definition. Any request or response that falls outside the contract gets blocked.
This differs from traditional WAFs that rely on signature-based detection of known attack patterns.
When deployed as a sidecar proxy in Kubernetes pods, 42Crunch reports sub-millisecond latency overhead. The firewall also runs on standalone deployments outside container orchestrators.
API Contract Generator
A newer addition to the platform, the API Contract Generator converts existing Postman Collections and HAR (HTTP Archive) files into OpenAPI definitions. It processes up to 10 input files (250 MB combined) and runs directly in VS Code and JetBrains IDEs.
This is useful for teams that have APIs running without formal OpenAPI documentation — generating the spec is the first step toward auditing and protecting them.
What does 42Crunch integrate with?
IDE Extensions
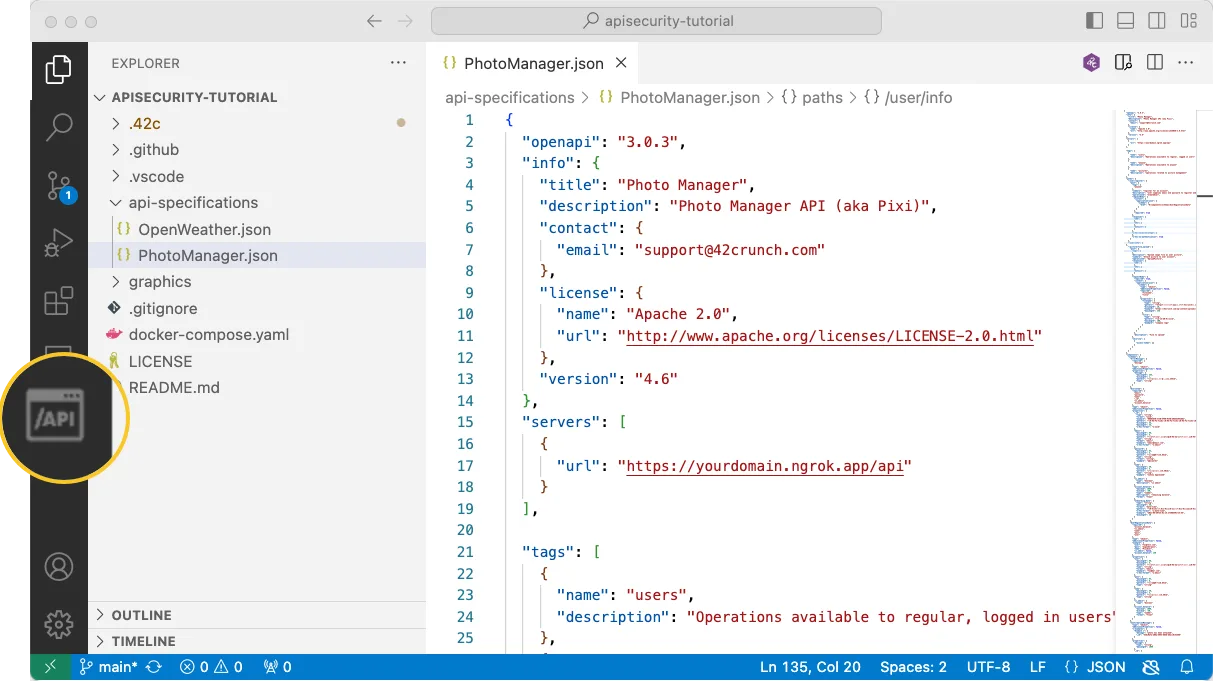
42Crunch’s IDE extensions have been used by over 1.6 million developers worldwide as of November 2025. They support Security Audit, Conformance Scan, and the API Contract Generator.
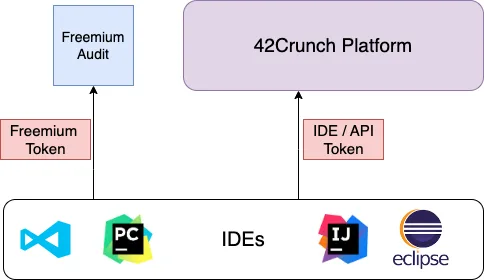
Three execution modes are available in the IDE:
- Freemium — stateless centralized service with usage limits, no account needed
- Local CLI — runs the 42Crunch AST binary locally
- Platform — connects to the full 42Crunch SaaS platform via IDE tokens
The VS Code extension includes an OpenAPI editor with IntelliSense, code navigation, SwaggerUI/ReDoc preview, and a “Try It” feature for testing API operations directly from the editor.
CI/CD Pipelines
A generic Docker image is also available for CI/CD platforms not on this list.
The GitHub Actions integration (42Crunch/api-security-audit-action ) runs static security testing on OpenAPI files, sets minimum score thresholds, and uploads findings to GitHub Code Scanning alerts as SARIF reports.
Cloud Marketplaces
42Crunch is available on the Microsoft Azure Marketplace and integrates with Microsoft Defender for Cloud.
How do I get started with 42Crunch?
.json and .yaml files that contain OpenAPI definitions. Use the OpenAPI Explorer panel to navigate the structure.For the full platform (CI/CD gates, runtime protection, team dashboards), create an account at 42crunch.com and generate an API token for your integrations.
When to use 42Crunch
42Crunch fits teams that already use OpenAPI specifications or are willing to adopt them. The entire platform revolves around the OpenAPI contract, so teams without formal API documentation need to create specs first (the Contract Generator helps with that).
It works well when:
- Your APIs have OpenAPI definitions and you want automated security scoring in the IDE and CI/CD pipeline
- You need a runtime firewall that enforces the API contract, not just signature-based blocking
- You want to shift API security left into the development workflow rather than testing only after deployment
- Compliance requirements demand documented, tested, and enforced API security policies
It is probably not the right fit when:
- Your APIs lack formal OpenAPI definitions and you do not plan to create them
- You need traffic-based API discovery as the primary feature — 42Crunch focuses on spec-driven security, not network traffic analysis
- You want a standalone DAST scanner — consider tools like Invicti or APIsec instead
How to use 42Crunch
The fastest path to value treats the IDE extension as the entry point and works outward from there. I usually walk teams through five steps.
First, author or import an OpenAPI spec. If your services do not yet have one, the API Contract Generator can convert Postman Collections or HAR captures into a v3 OpenAPI document. The accuracy depends on how representative the input traffic was, so this is a starting draft, not a final contract.
Second, install the 42Crunch extension in VS Code, JetBrains, or Eclipse and open the spec. The Security Audit runs locally against the freemium service and returns a score plus inline issues with quick-fix suggestions for security definitions and data validation gaps.
Third, wire the audit into CI. The official GitHub Actions integration (42Crunch/api-security-audit-action ) accepts a minimum score threshold — pull requests that drop the score below the gate fail the build. SARIF output uploads to GitHub code-scanning alerts so findings sit alongside the rest of your AppSec data.
Fourth, run the Conformance Scan against a non-production deployment of the API. The scan generates real HTTP traffic and compares actual responses to the contract. Drift Scan is the only mode 42Crunch approves for production use.
Finally, deploy the micro API firewall as a sidecar in front of the API to enforce the contract at runtime. Sub-millisecond latency overhead is the documented overhead in Kubernetes deployments.
How much does 42Crunch cost?
42crunch.com publishes four tiers, which is unusually transparent for an enterprise API security vendor. The model is operation-metered rather than user-seat dominant.
The Free tier costs nothing and runs entirely inside the IDE. It includes 100 operations per month each for Contract Generator, Audit, and Scan and is single-user only.
The Single User tier starts from $7.50 per month and lifts the operation limits to 2,000 per month for each capability. It still runs in the IDE without a platform account.
The Teams tier starts from $375 per month, requires a minimum of five users and seventy-five endpoints, and unlocks the SaaS platform — collaboration features, unlimited testing on contracted endpoints, and CI/CD integration. Runtime protection (the micro API firewall) is an optional add-on at this tier.
The Enterprise tier is contact-sales pricing with a minimum of twenty users and two hundred fifty endpoints. It bundles unlimited testing, API gateway integrations, SIEM/SOC connectors, and a structured proof-of-concept process.
For most teams the Teams tier is where 42Crunch starts to look like a platform investment rather than a developer tool. Smaller projects that just need design-time auditing usually stay in the Free or Single User tier indefinitely.
What are alternatives to 42Crunch?
42Crunch occupies a narrow but defensible slot: contract-first, design-time-leaning API security. The closest substitutes pivot on different axes.
APIsec leads with automated API penetration testing rather than spec audit. If your team would rather scan the running API for OWASP API Top 10 issues than enforce the OpenAPI contract upstream, APIsec covers that workflow with a heavier emphasis on reporting.
Salt Security sits at the opposite end of the spectrum — runtime, behavior-based, and fed by mirrored production traffic. Salt is the canonical choice when you do not have OpenAPI specs and never will, since it learns endpoints from network observation instead of contracts.
Akamai API Security (formerly Noname Security, acquired in June 2024 for $450M) extends the Akamai edge into API discovery and runtime posture. It is a fit when you already run on Akamai’s CDN and want API protection bundled with WAF and bot management.
Wallarm brings a WAAP heritage to API security with an API discovery layer on top. It blocks at the edge, which puts it closer to Akamai than to 42Crunch in terms of architecture.
Imperva API Security follows the same WAF-extending pattern as Akamai. The platform leans on Imperva’s existing application security stack rather than starting from API contracts.
For a deeper one-on-one comparison, see Salt Security vs 42Crunch .